DeepSeek's Cybersecurity Woes: Exposed Database Raises Serious Concerns
3 Sources
3 Sources
[1]
Deep trouble: Infosec firm finds a DeepSeek database 'completely open and unauthenticated' exposing chat history, API keys, and operational details
DeepSeek has been the name on everyone's lips this week, as the release of its R1 AI model spooked the tech market and caused significant financial losses for several major players. Concerns have been raised regarding the security of the Chinese AI startup and its models -- and if reports regarding an open database are to be believed, those claims may have some merit. New York-based cloud security provider Wiz has issued an advisory claiming its research wing identified a publicly accessible ClickHouse database, belonging to DeepSeek, left "completely open and unauthenticated" (via The Register). The database was said to have been discovered within minutes of the Wiz research team's investigation into DeepSeek's cybersecurity resilience and it contained "a significant volume of chat history, backend data, and sensitive information." Worse still, the database was so completely unprotected that it was possible to gain full database control and privilege escalation from inside the environment, with no authentication or defence mechanism present. A potential attacker could have easily obtained plaintext passwords, local files, and proprietary data with a simple SQL command. Wiz duly informed DeepSeek of the open database, which it says was promptly secured. As word of DeepSeek's efforts has spread throughout the tech industry, so have potential data security concerns from multiple sources. Data regulators from the UK, Italy, Ireland and Australia have all begun enquiries into the practices of the company, while OpenAI has complained that DeepSeek has been copying its models. The US Navy has issued a warning to its members to avoid using DeepSeek "in any capacity", while the US National Security Council says it's looking into the security implications of the DeepSeek app. AI security provider HiddenLayer claims that DeepSeek-R1 is "vulnerable to jailbreak techniques, prompt injections, glitch tokens, and exploitation of its control tokens, making it less secure than other modern LLMs." Given the disruptive nature of DeepSeek's entry into the market, it's difficult to ascertain how many of these claims are legitimate, and how many may be reactionary attempts looking to restore some of the AI status quo. Regardless, leaving a database wide open to be manipulated by any who may come prying is not a great look. It seems like no matter what happens next, DeepSeek will be at the top of everyone's AI concerns for a while to come.
[2]
DeepSeek's Database Might Have Been Leaked Exposing Chat History
It is said to contain chat history, secret keys, and backend details DeepSeek's dataset might have suffered public exposure, claimed a cybersecurity research firm. As per a report, a publicly accessible ClickHouse database belonging to DeepSeek was discovered which allowed full control over its database operations. Additionally, the exposure is also said to contain a large volume of sensitive information including chat history, secret keys, log times, and backend details. It is unclear whether the firm reported the matter to the Chinese AI firm, and if the exposed dataset has been taken down. In a blog post, cybersecurity firm Wiz Research revealed that it found a completely open and unauthenticated dataset that contained highly sensitive information about the DeepSeek platform. The exposed information is said to pose a potential risk to both the AI firm as well as the end users. The cybersecurity firm claimed that it intended to assess DeepSeek's external security to identify any potential vulnerabilities, given the rising popularity of the AI platform. The researchers started by mapping any Internet-facing subdomains but did not find anything that could suggest a high-risk exposure. However, after implementing new techniques, the researchers were able to detect two open ports (8123 and 9000) associated with multiple public hosts. Wiz Research claimed that these ports led them to a publicly exposed ClickHouse database which could be accessed without any authentication. Notably, ClickHouse is an open-source, columnar database management system developed by Yandex. It is used for fast analytical queries and is often used by ethical hackers to scan the dark web for exposed data. A log stream table in the dataset is claimed to contain more than one million log entries including timestamps with logs from January 6, references to multiple internal DeepSeek application programming interface (API) endpoints, as well as chat history, API Keys, backend details, and operational metadata in plain-text. The researchers claimed that with this level of information, a bad actor could potentially exfiltrate passwords, local files, and proprietary information directly from the server. At the time of writing this, there was no update on whether this data exposure can be contained and whether the dataset can be taken offline.
[3]
DeepSeek report raises serious doubts about its security
The lack of security not only left sensitive data exposed, but also made it possible for outsiders to take full control of the database and escalate privileges within DeepSeek's environment. Chinese startup DeepSeek caught a lot of people off guard with the sudden emergence of its R1 AI model. Capable of going toe-to-toe with rivals like OpenAI's ChatGPT and Meta's Llama, yet trained at a fraction of the cost, it became the talk of the town and quickly jumped to number one in the top free apps in the Apple App Store in the US (#10 in the Play Store). Shortly after its meteoric rise in popularity, it was hit by a large-scale cyberattack. After an investigation into the company's cybersecurity, it's kind of surprising a cyberattack didn't happen sooner.
Share
Share
Copy Link
A cybersecurity firm discovers an unprotected DeepSeek database, exposing sensitive information and raising questions about the AI startup's security practices.

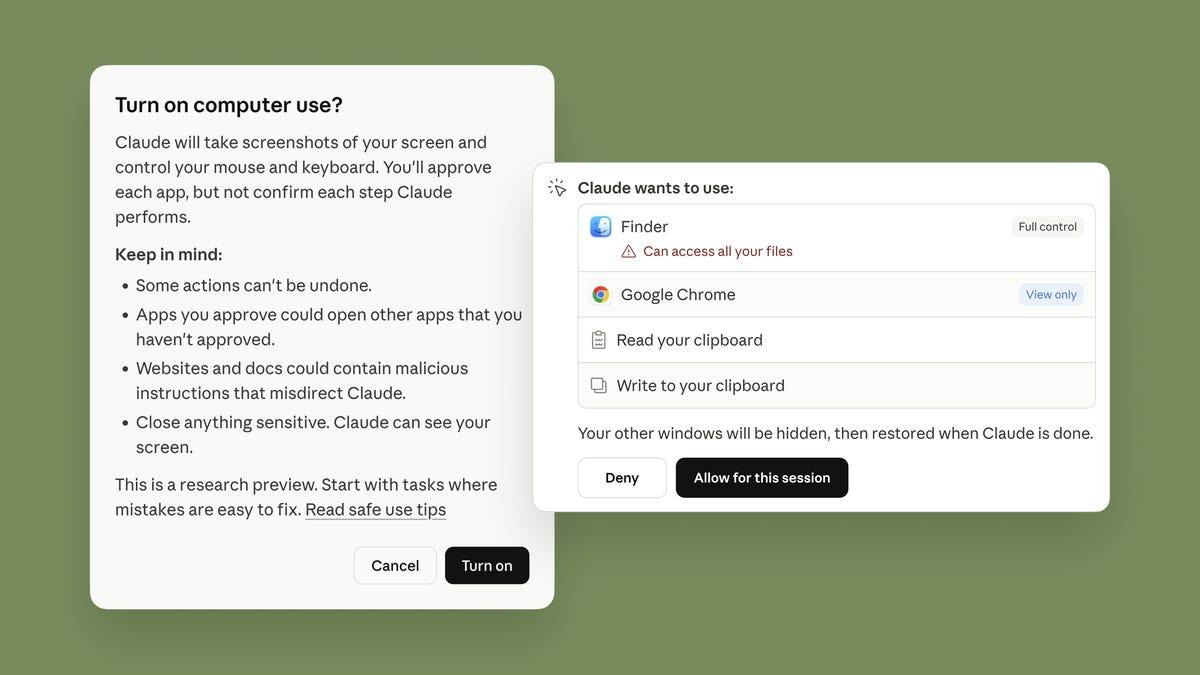
DeepSeek's Unsecured Database Discovered
In a startling revelation, New York-based cloud security provider Wiz has uncovered a significant security lapse in DeepSeek's infrastructure. The Chinese AI startup, which recently made waves with its R1 AI model, left a ClickHouse database "completely open and unauthenticated," exposing sensitive information to potential attackers
1
.Extent of the Exposure
The exposed database contained a wealth of sensitive information, including:
- Chat history
- Backend data
- API keys
- Operational metadata
- Plaintext passwords
- Local files
- Proprietary information
Wiz researchers claim that the database was so poorly protected that it allowed for full database control and privilege escalation within DeepSeek's environment, all without any authentication or defense mechanisms
2
.Discovery and Implications
The security flaw was identified within minutes of Wiz's investigation into DeepSeek's cybersecurity resilience. The researchers found two open ports (8123 and 9000) associated with multiple public hosts, leading them to the exposed ClickHouse database
2
.This discovery raises serious concerns about DeepSeek's security practices, especially given the company's rapid rise to prominence. The R1 AI model's sudden emergence and ability to compete with established players like OpenAI's ChatGPT and Meta's Llama had already drawn attention to the company
3
.Related Stories
Broader Security Concerns
The incident has sparked wider discussions about DeepSeek's overall security:
- Data regulators from the UK, Italy, Ireland, and Australia have initiated inquiries into the company's practices.
- OpenAI has accused DeepSeek of copying its models.
- The US Navy has warned its members against using DeepSeek "in any capacity."
- The US National Security Council is investigating the security implications of the DeepSeek app.
AI security provider HiddenLayer claims that DeepSeek-R1 is vulnerable to various exploitation techniques, including jailbreak methods, prompt injections, and glitch tokens
1
.Industry Impact
DeepSeek's security lapse comes at a critical time for the AI industry. The company's R1 model had already caused significant market disruption, leading to financial losses for several major tech players. This incident is likely to intensify scrutiny of AI startups and their security measures, potentially influencing investor confidence and regulatory approaches in the rapidly evolving AI sector.
References
Summarized by
Navi
[3]
Related Stories
Recent Highlights
1
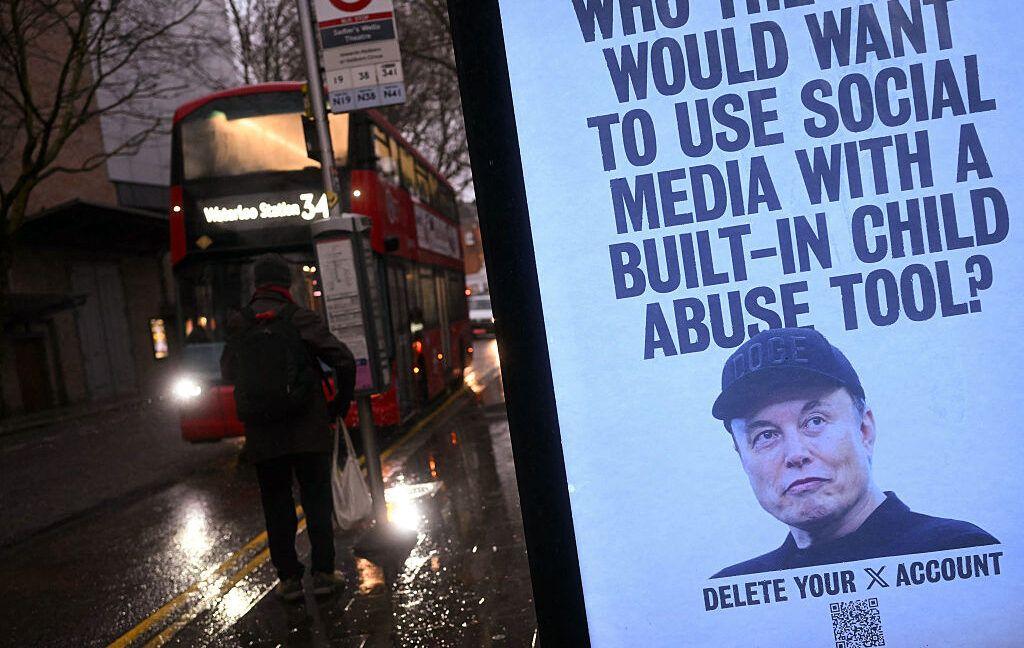
Tennessee Teens Sue Elon Musk's xAI Over Grok AI-Generated Child Abuse Images
Policy and Regulation
2
Supermicro Co-Founder Indicted in $2.5 Billion Nvidia AI Chip Smuggling Scheme to China
Policy and Regulation

3
Val Kilmer to appear posthumously in As Deep as the Grave through AI-generated performance
Entertainment and Society