AI Coding Assistant Cline Hit by Supply Chain Attack That Installed OpenClaw on Developers' Machines
2 Sources
2 Sources
[1]
AI coding assistant Cline compromised, installs OpenClaw
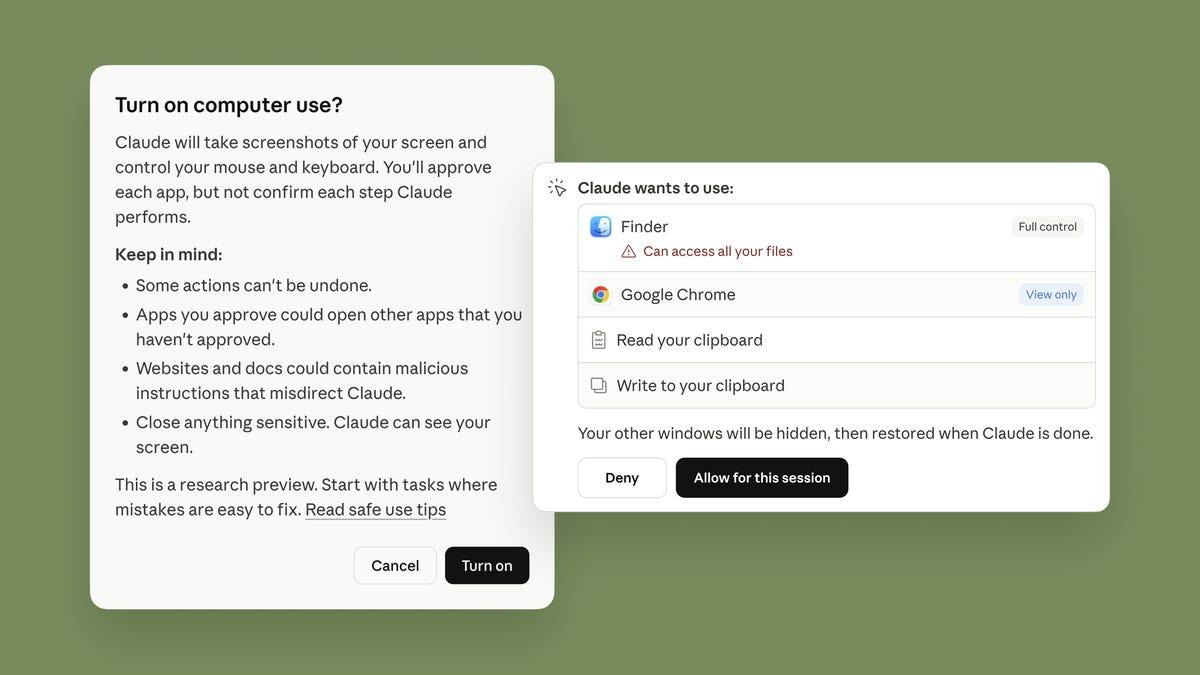
Someone compromised open source AI coding assistant Cline CLI's npm package earlier this week in an odd supply chain attack that secretly installed OpenClaw on developers' machines without their knowledge. The incident occurred on Tuesday, when an "unauthorized party" used a compromised token to publish an update to Cline CLI on its npm registry that installs OpenClaw - the AI agent platform slash security nightmare - on users' computers when they install [email protected]. "Users who installed Cline CLI [email protected] during the approximately 8-hour window between 3:26 AM PT and 11:30 AM PT on February 17 will have openclaw globally installed," Cline's maintainers said in a security advisory. "The openclaw package is a legitimate open source project and is not malicious, but its installation was not authorized or intended." The maintainers also revoked the compromised token, and added that "npm publishing now uses OIDC provenance via GitHub Actions." Anyone who installed Cline during this time period should update to a fixed version (2.4.0 or higher) and check their environment for a surprise OpenClaw installation. Earlier this month, security researcher Adnan Khan found and disclosed a prompt injection vulnerability (since fixed) to Cline that could be abused for this exact purpose. "To make sure it's clear in the midst of the NPM package situation: I did NOT conduct overt testing on Cline's repository," Khan said in an update to his research. "I conducted my PoC on a mirror of Cline to confirm the prompt injection vulnerability," he added. "A different actor found my PoC on my test repository and used it to directly attack Cline and obtain the publication credentials." Microsoft did note a "small but noticeable uptick in installations of OpenClaw initiated by Cline CLI installation script" during the eight-hour supply chain incident on February 17. StepSecurity, meanwhile, reported that the compromised version was downloaded about 4,000 times before the package maintainers deprecated it. We don't know who's responsible for slipping OpenClaw into Cline's npm registry - and for what purposes other than creating more chaotic AI agents. ®
[2]
Cline CLI 2.3.0 Supply Chain Attack Installed OpenClaw on Developer Systems
In yet another software supply chain attack, the open-source, artificial intelligence (AI)-powered coding assistant Cline CLI was updated to stealthily install OpenClaw, a self-hosted autonomous AI agent that has become exceedingly popular in the past few months. "On February 17, 2026, at 3:26 AM PT, an unauthorized party used a compromised npm publish token to publish an update to Cline CLI on the NPM registry: [email protected]," the maintainers of the Cline package said in an advisory. "The published package contains a modified package.json with an added postinstall script: 'postinstall": "npm install -g openclaw@latest.'" As a result, this causes OpenClaw to be installed on the developer's machine when Cline version 2.3.0 is installed. Cline said no additional modifications were introduced to the package and there was no malicious behavior observed. However, it noted that the installation of OpenClaw was not authorized or intended. The supply chain attack affects all users who installed the Cline CLI package published on npm, specifically version 2.3.0, during an approximately eight-hour window between 3:26 a.m. PT and 11:30 a.m. PT on February 17, 2026. The incident does not impact Cline's Visual Studio Code (VS Code) extension and JetBrains plugin. To mitigate the unauthorized publication, Cline maintainers have released version 2.4.0. Version 2.3.0 has since been deprecated and the compromised token has been revoked. Cline also said the npm publishing mechanism has been updated to support OpenID Connect (OIDC) via GitHub Actions. In a post on X, the Microsoft Threat Intelligence team said it observed a "small but noticeable uptick" in OpenClaw installations on February 17, 2026, as a result of the supply chain compromise of the Cline CLI package. According to StepSecurity, the compromised Cline package was downloaded roughly 4,000 times during the eight-hour stretch. Users are advised to update to the latest version, check their environment for any unexpected installation of OpenClaw, and remove it if not required. "Overall impact is considered low, despite high download counts: OpenClaw itself is not malicious, and the installation does not include the installation/start of the Gateway daemon," Endor Labs researcher Henrik Plate said. "Still, this event emphasizes the need for package maintainers to not only enable trusted publishing, but also disable publication through traditional tokens - and for package users to pay attention to the presence (and sudden absence) of corresponding attestations." While it's currently not clear who is behind the breach of the npm package and what their end goals were, it comes after security researcher Adnan Khan discovered that attackers could steal the repository's authentication tokens through prompt injection by taking advantage of the fact that it is configured to automatically triage any incoming issue raised on GitHub. "When a new issue is opened, the workflow spins up Claude with access to the repository and a broad set of tools to analyze and respond to the issue," Khan explained. "The intent: automate first-response to reduce maintainer burden." But a misconfiguration in the workflow meant that it gave Claude excessive permissions to achieve arbitrary code execution within the default branch. This aspect, combined with a prompt injection embedded within the GitHub issue title, could be exploited by an attacker with a GitHub account to trick the AI agent into running arbitrary commands and compromise production releases. This shortcoming, which builds up PromptPwnd, has been codenamed Clinejection. It was introduced in a source code commit made on December 21, 2025. The attack chain is outlined below - "This would allow an attacker to obtain code execution in the nightly workflow and steal the publication secrets," Khan noted. "If a threat actor were to obtain the production publish tokens, the result would be a devastating supply chain attack." "A malicious update pushed through compromised publication credentials would execute in the context of every developer who has the extension installed and set to update automatically." In other words, the attack sequence employs GitHub Actions cache poisoning to pivot from the triage workflow to a highly privileged workflow, such as the Publish Nightly Release and Publish NPM Nightly workflows, and steal the nightly publication credentials, which have the same access as those used for production releases. As it turns out, this is exactly what happened, with the unknown threat actor weaponizing an active npm publish token (referred to as NPM_RELEASE_TOKEN or NPM_TOKEN) to authenticate with the Node.js registry and publish Cline version 2.3.0. "We have been talking about AI supply chain security in theoretical terms for too long, and this week it became an operational reality," Chris Hughes, VP of Security Strategy at Zenity, said in a statement shared with The Hacker News. "When a single issue title can influence an automated build pipeline and affect a published release, the risk is no longer theoretical. The industry needs to start recognizing AI agents as privileged actors that require governance."
Share
Share
Copy Link
The open-source AI coding assistant Cline fell victim to a software supply chain attack on February 17, 2026, when attackers used a compromised npm token to publish a malicious update. The breach installed OpenClaw—an autonomous AI agent platform—on approximately 4,000 developer systems during an eight-hour window. Security researchers traced the attack to a prompt injection vulnerability that allowed threat actors to steal publication credentials.
Compromised NPM Token Triggers Eight-Hour Security Incident
An unauthorized party exploited a compromised npm token to publish Cline version 2.3.0 on February 17, 2026, at 3:26 AM PT, triggering a supply chain attack that affected developer systems worldwide
1
. The AI coding assistant Cline, a popular open source project, became the latest victim in a growing wave of software supply chain attacks targeting the development community. Users who installed the compromised npm package during the approximately eight-hour window between 3:26 AM PT and 11:30 AM PT unknowingly received OpenClaw installations on their machines2
.
Source: Hacker News
The malicious update modified the package.json file to include a postinstall script that executed "npm install -g openclaw@latest," causing the autonomous AI agent platform to install globally whenever developers added Cline CLI [email protected] to their systems
2
. StepSecurity reported that the compromised version was downloaded approximately 4,000 times before Cline maintainers deprecated it and released version 2.4.0 as a fix1
.Prompt Injection Vulnerability Enabled Credential Theft
The attack chain began with a prompt injection vulnerability discovered by security researcher Adnan Khan, who found that attackers could steal the repository's authentication tokens through a flaw in Cline's GitHub Actions workflow
2
. The vulnerability, codenamed Clinejection, emerged from a misconfiguration introduced in a source code commit made on December 21, 2025, which gave Claude AI excessive permissions to achieve arbitrary code execution within the default branch2
.Khan clarified that he conducted his proof-of-concept testing on a mirror of Cline to confirm the prompt injection vulnerability, not on the actual repository
1
. However, a different threat actor discovered his PoC on the test repository and weaponized it to directly attack Cline and obtain the publication credentials. The attack sequence employed GitHub Actions cache poisoning to pivot from the triage workflow to highly privileged workflows, including the Publish Nightly Release and Publish NPM Nightly workflows, ultimately stealing the nightly publication credentials2
.Microsoft Confirms Uptick in OpenClaw Installations
Microsoft Threat Intelligence observed a "small but noticeable uptick in installations of OpenClaw initiated by Cline CLI installation script" during the eight-hour supply chain incident on February 17
1
. While OpenClaw itself is a legitimate open source project and not inherently malicious, its unauthorized installation raises significant concerns about AI supply chain security and the potential for more damaging attacks using similar techniques1
.Endor Labs researcher Henrik Plate assessed the overall impact as "considered low, despite high download counts," noting that OpenClaw itself is not malicious and the installation does not include the installation or start of the Gateway daemon
2
. However, the incident demonstrates the vulnerability of developer systems to sophisticated attacks that exploit AI-powered workflows.Related Stories
Enhanced Security Measures Implemented
Cline maintainers responded swiftly by revoking the compromised token and implementing OIDC provenance via GitHub Actions for npm publishing
1
. The incident does not impact Cline's Visual Studio Code extension and JetBrains plugin, only affecting the npm registry package2
. Users are advised to update to version 2.4.0 or higher and check their environment for unexpected OpenClaw installations.Chris Hughes, VP of Security Strategy at Zenity, emphasized the gravity of the situation: "We have been talking about AI supply chain security in theoretical terms for too long, and this week it became an operational reality"
2
. The event underscores the need for package maintainers to not only enable trusted publishing but also disable publication through traditional tokens, while package users must pay attention to the presence and sudden absence of corresponding attestations. As AI agents gain more autonomy in development workflows, the attack surface expands, making prompt injection vulnerabilities a critical concern for organizations relying on AI coding assistants.References
Summarized by
Navi
[1]
Related Stories
OpenClaw security crisis deepens as 135,000+ instances exposed and malware floods marketplace
04 Feb 2026•Technology

OpenClaw security vulnerability lets malicious websites hijack AI agents in 'ClawJacked' attack
03 Mar 2026•Technology
Infostealer malware targets OpenClaw AI agents, stealing API keys and authentication tokens
16 Feb 2026•Technology

Recent Highlights
1
Tennessee Teens Sue Elon Musk's xAI Over Grok AI-Generated Child Abuse Images
Policy and Regulation
2
Supermicro Co-Founder Indicted in $2.5 Billion Nvidia AI Chip Smuggling Scheme to China
Policy and Regulation

3
Val Kilmer to appear posthumously in As Deep as the Grave through AI-generated performance
Entertainment and Society