Chrome Gemini vulnerability allowed malicious extensions to hijack AI and spy on users
3 Sources
3 Sources
[1]
This high-severity Chrome Gemini vulnerability lets malicious extensions spy on your PC
It grants extensions the ability to spy on you or steal your data. A new vulnerability impacting Google Chrome's Gemini agentic AI feature has been disclosed -- patch now to stay protected. Also: AI agents are fast, loose, and out of control, MIT study finds Disclosed by senior principal security researcher Gal Weizman from Palo Alto Networks' Unit 42 team, the browser vulnerability affects Google Chrome's Gemini AI feature, an artificial intelligence (AI) agentic browser assistant. Tracked as CVE-2026-0628 and deemed high severity, the vulnerability is described as an "insufficient policy enforcement in WebView tag in Google Chrome" issue that, prior to version 143.0.7499.192 of the browser, "allowed an attacker who convinced a user to install a malicious extension to inject scripts or HTML into a privileged page via a crafted Chrome Extension." Also: Why scammers say nothing when they call - and how to respond safely The team found that an extension with access to a basic permission set, via the declarativeNetRequests API, could grant permissions that an attacker could exploit to inject JavaScript code into the new Gemini panel browser component. According to the researchers, this vulnerability can be used as part of a broader attack chain targeting Google Chrome users. If, for example, an attacker can convince a target to download and install an innocent-looking browser extension, a malicious extension could exploit the policy problem to hijack Gemini. The AI assistant may then take action without permission, including granting a cybercriminal access to webcams and microphones, taking screenshots, and accessing local files and directories. The panel could also be hijacked for phishing purposes. "Since the Gemini app relies on performing actions for legitimate purposes, hijacking the Gemini panel allows privileged access to system resources that an extension would not normally have," the researchers said. Following Palo Alto Networks' private disclosure to Google in October last year, it's been up to the team to triage, replicate, and patch the bug. Included in Google Chrome's January patch notes, the Chrome security team developed a fix and included it in the 143.0.7499.192/.193 Windows and macOS stable channels (143.0.7499.192 for Linux). There have been additional security patches rolled out since, including fixes for vulnerabilities such as out-of-bounds bugs. Also: Destroyed servers and DoS attacks: What can happen when OpenClaw AI agents interact The best advice is simple: as soon as you see an alert that a new version of Chrome is available -- usually to the right of your address bar on desktop -- accept the update. Not only can you benefit from performance improvements and new features, but the patches included in these releases will mitigate the risk of your browser and data becoming compromised. Agentic browsers may very well be the benchmark for browser experiences in the future. However, while they are still being developed, we are encountering new cybersecurity challenges that are increasing the attack surface and placing our privacy and data at risk. Agentic AI features, typically framed through messaging and chat windows, aim to provide value by answering our queries, sourcing information on our behalf, filling out forms for us, and helping us manage our workflows. But the security ramifications of giving often untried, untested, and insecure AI-driven tools the keys to online accounts and services -- not to mention the power to act on our behalf -- have caused a security nightmare for defenders. Also: Microsoft and ServiceNow's exploitable agents reveal a growing - and preventable - AI security crisis Why are they worried? Aside from the usual vulnerabilities, disclosures, and patch management that are necessary for software today, AI browsers and agents can be susceptible to prompt-injection attacks. Malicious instructions can be hidden in source material and websites, which then hijack these tools, forcing them to hand over a user's sensitive information, conduct surveillance, and perform all manner of illicit activities. There's also the question of trust. Just how much should you trust an AI system with personal data, and if it were exposed or leaked, what would the ramifications be for you? A recent MIT study found serious gaps in the "fast and loose" agentic AI development race regarding security testing, and so such technologies must be treated with caution. Also: This new phone scam has 'carriers' calling to exchange your device - don't fall for it We've yet to see the full security risks that agentic AI will pose, but we also have yet to see its true potential. Managing its benefits while balancing risk will be the true challenge -- and this applies to both consumers and businesses. "Innovation can't come at the expense of security," commented Anupam Upadhyaya, SVP, Product Management, Prisma SASE, Palo Alto Networks. "If organizations choose to deploy agentic browsers, they must treat them as high-risk infrastructure, with runtime visibility, enforced policy controls, and hardened guardrails built in from day one. Anything less invites compromise."
[2]
Chrome AI panel became privilege escalator for extensions
High-severity flaw let malicious add-ons access system via browser's embedded AI feature Security boffins have discovered a high-severity bug in Google Chrome that allowed malicious extensions to hijack its Gemini Live AI panel and inherit privileges they were never meant to have. The flaw, tracked as CVE-2026-0628, was uncovered by researchers at Palo Alto Networks' Unit 42 who found that rogue Chrome extensions could manipulate how the browser handled requests to the embedded Gemini Live side panel. By exploiting the way Chrome handles extension network rules, a malicious add-on with fairly standard permissions could intercept and tamper with traffic headed for the Gemini panel, slipping its own JavaScript into a far more trusted part of the browser. Gemini Live, built into Chrome as an interactive AI panel, isn't just a chatbot bolted onto a tab. It's tightly integrated into the browser to grab screenshots, read local files, and turn on your camera or microphone when asked. That's handy if you're using it as intended, but less so if a sketchy extension manages to ride along and inherit the same level of access, stepping well beyond the permissions add-ons are supposed to have. "Since the Gemini app relies on performing actions for legitimate purposes, hijacking the Gemini panel allows privileged access to system resources that an extension would not normally have," said Gal Weizman, security researcher at Palo Alto Networks. In effect, a malicious extension could have turned on a webcam or microphone, sifted through local files, taken screenshots, or slipped phishing messages into what appears to be a legitimate Gemini panel. Nothing particularly fancy was required - just ordinary extension behavior bumping up against a flaw in how Chrome walled off its AI feature. Google fixed the bug in early January, shipping patches in Chrome 143.0.7499.192 and 143.0.7499.193 for desktop via a Stable Channel update. The hole was closed before Unit 42 went public, and anyone on a current version is covered. Even so, it's yet another example of how deeply integrating AI features with core software can quietly reshape the browser's threat model. News of the bug comes after analyst firm Gartner advised most organizations to avoid so-called "agentic" browsers, arguing that AI-driven automation with deep system hooks introduces risks that outweigh the productivity upside for many enterprises. It also follows fresh evidence that attackers are already experimenting with generative AI inside their tooling. In February, researchers detailed Android malware that tapped Google's Gemini model at runtime to help interpret screenshots and automate on-device actions, showing that criminals are just as keen as vendors to wire AI into sensitive parts of the stack. For years, browser makers have tried to keep extensions boxed in so one bad download can't poke around your system. Add an AI helper that's allowed to read files and tap your mic on command, and things get messier. This bug is a fairly simple reminder: the more power you give software in the name of convenience, the more careful you have to be about who else might get their hands on it. ®
[3]
Google Chrome Patch Signals Need for Constant AI Browser Vigilance | PYMNTS.com
By completing this form, you agree to receive marketing communications from PYMNTS and to the sharing of your information with our sponsor, if applicable, in accordance with our Privacy Policy and Terms and Conditions. This new browser architecture introduces an AI assistant that could allow attackers to issue commands to the browser core, according to the post. In addition, the integration of an AI side panel brings about vulnerabilities that could be exploited by less-privileged website or browser panels, per the post. In order to perform tasks, AI browsers must be granted privileged access to the browsing environment so they can see what the user sees on the screen and get information from the website, according to the post. "However, this expanded capability and privileged access introduce a new and widened attack surface," the post said. "This creates security implications that are not present in traditional browsers." Unit 42 said this while outlining a security vulnerability in Google's Gemini feature in its Chrome browser that was discovered and fixed. This security vulnerability, CVE-2026-0628, could have allowed malicious extensions with basic permissions to take control of the Gemini Live in Chrome browser panel, escalate privileges, and perform actions such as access the victim's camera and microphone, take screenshots of websites and access local files and directories, according to the post. Unit 42 uncovered the security vulnerability, disclosed it to Google and helped the company remediate it, per the post. Google released a fix in early January before the information about the security vulnerability was published. "While AI browsers or AI features implemented into existing browsers can improve the user experience, it's important to continue monitoring for potential security flaws," the post said. It was reported in February that Google's Chrome web store is being plagued by a wave of malicious browser extensions that claim to offer the abilities of an AI assistant but steal users' personal information in secret. PYMNTS reported in October 2025 that the autonomy that makes AI browsers powerful also makes them risky. Google said in a December 2025 blog post that it designed new tools it will use to improve the safety of agentic browsing with Chrome.
Share
Share
Copy Link
A high-severity vulnerability in Google Chrome's Gemini AI feature let malicious browser extensions escalate privileges and access system resources like webcams, microphones, and local files. Discovered by Palo Alto Networks, CVE-2026-0628 was patched in January, but it highlights growing security risks of agentic AI integration in browsers.
High-Severity Chrome Vulnerability Exposed Gemini AI to Exploitation
A Chrome Gemini vulnerability tracked as CVE-2026-0628 has revealed how deeply AI integration in browsers can reshape the threat model for users. Discovered by Gal Weizman, senior principal security researcher at Palo Alto Networks' Unit 42 team, the flaw allowed malicious browser extensions with basic permissions to hijack Google Chrome's Gemini Live AI panel and gain unauthorized access to system resources they were never meant to control
1
. The vulnerability was classified as high-severity and described as "insufficient policy enforcement in WebView tag in Google Chrome" that existed prior to version 143.0.7499.192 of the browser1
.
Source: The Register
How Malicious Browser Extensions Exploited the Gemini AI Agentic Browser Feature
The privilege escalation vulnerability worked by exploiting how Google Chrome handled extension network rules through the declarativeNetRequests API. A rogue extension with fairly standard permissions could intercept and tamper with traffic headed for the Gemini Live side panel, injecting JavaScript code into what should have been a privileged browser component
2
. Since the Gemini AI agentic browser feature is tightly integrated into Chrome to perform legitimate actions like capturing screenshots, reading local files, and activating webcam and microphone access, hijacking this panel granted extensions the same elevated privileges2
.An attacker who convinced a target to install an innocent-looking extension could exploit this policy problem to conduct surveillance, steal data, access local files and directories, or even deploy phishing attacks through what appeared to be a legitimate Gemini panel
1
. "Since the Gemini app relies on performing actions for legitimate purposes, hijacking the Gemini panel allows privileged access to system resources that an extension would not normally have," Unit 42 researchers explained2
.
Source: ZDNet
Patch Released After Private Disclosure to Google
Following Palo Alto Networks' private disclosure to Google in October last year, the Chrome security team developed a fix and included it in version 143.0.7499.192/.193 for Windows and macOS stable channels, with version 143.0.7499.192 for Linux
1
. The patch was released in early January before Unit 42 publicly disclosed the vulnerability3
. Users should accept browser updates immediately when prompted to benefit from security patches that mitigate the risk of browser and data compromise1
.Related Stories
Security Risks of Agentic AI Create Expanded Attack Surface
This vulnerability underscores the security risks of agentic AI and the cybersecurity challenges that emerge when AI-driven tools receive privileged access to online accounts and system resources. AI integration in browsers requires these features to see what users see on screen and extract information from websites, creating an expanded attack surface that traditional browsers don't face
3
. Beyond conventional vulnerabilities requiring patch management, AI browsers can be susceptible to prompt injection attacks where malicious instructions hidden in source material hijack these tools to hand over sensitive information or conduct surveillance1
.Analyst firm Gartner has advised most organizations to avoid so-called agentic browsers, arguing that AI-driven automation with deep system hooks introduces risks that outweigh productivity benefits for many enterprises
2
. A recent MIT study found serious gaps in security testing during the "fast and loose" agentic AI development race, suggesting such technologies must be treated with caution1
. Researchers have also documented Android malware tapping Google's Gemini model at runtime to interpret screenshots and automate on-device actions, demonstrating that attackers are actively experimenting with generative AI inside their tooling2
.
Source: PYMNTS
What Users Should Watch For
The incident serves as a reminder that browser makers have worked for years to keep extensions boxed in so one bad download can't spy on your PC or access sensitive data. Adding an AI helper with permissions to read files and tap your microphone on command makes the threat model messier
2
. "While AI browsers or AI features implemented into existing browsers can improve the user experience, it's important to continue monitoring for potential security flaws," Unit 42 noted3
. Managing the benefits of agentic browsers while balancing risk will be the true challenge for both consumers and businesses as we've yet to see the full security implications these technologies will pose.References
Summarized by
Navi
[2]
Related Stories
Recent Highlights
1
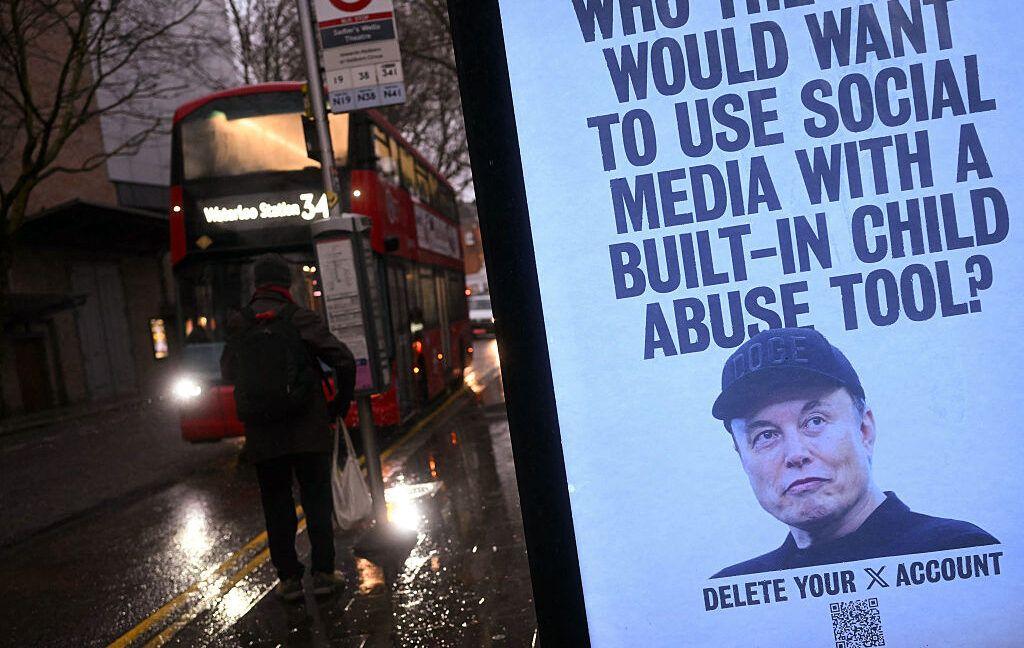
Tennessee Teens Sue Elon Musk's xAI Over Grok AI-Generated Child Abuse Images
Policy and Regulation
2
Pentagon designates Palantir Maven AI as core US military system in major defense shift
Technology

3
Supermicro Co-Founder Indicted in $2.5 Billion Nvidia AI Chip Smuggling Scheme to China
Policy and Regulation