Iran war exposes AI technology as new weapon in cyber warfare against U.S. and Israel
3 Sources
3 Sources
[1]
Old-school tricks and AI tech are weapons in the Iran war
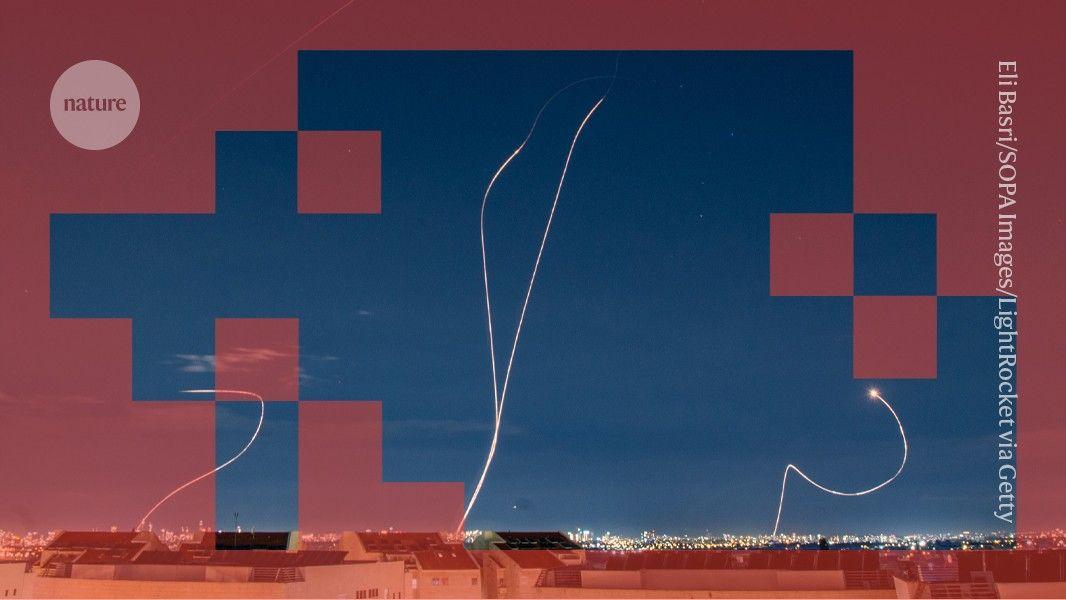
TEL AVIV, Israel -- In the nighttime hours before launching the Iran war, Israeli military generals made sure their cars were not in their usual parking spots at military headquarters in Tel Aviv, in case Iranian spotters were looking for clues that war was near. In the days before the war, U.S. warplanes were deliberately parked in southern Israel to distract Iran -- which was perhaps keeping a close eye with Chinese satellite imagery -- as Israel prepared its own fighter jets to take off from an entirely different location, the Ramat David base in northern Israel. These were some of the "white noise" tactics deployed as Israel and the U.S. launched the war against Iran, a senior Israeli defense official from the military's operations directorate told NPR. The official spoke on condition of anonymity to divulge some of Israel's shadowy tactics. "What usually you are doing is try to influence the thinking of the rival entity to let them think that the moment is not coming soon," said Col. (Res) Doron Hadar, who helped lead influence operations and psychological warfare for the Israeli military until recently. The Iran war is being fought on a hybrid digital-physical battlefield, with old-school deception tactics and cutting-edge AI technology, officials and analysts say. The U.S. military's very first move in the Iran war was in cyberspace. "Coordinated space and cyber operations effectively disrupted communications and sensor networks across the area of responsibility, leaving the adversary without the ability to see, coordinate, or respond effectively," Chairman of the Joint Chiefs of Staff Gen. Dan Caine told reporters. Israel's warplanes, sent to target Iranian Supreme Leader Ayatollah Ali Khamenei, located him thanks to Israel's hacking of traffic cameras in the Iranian capital, the senior Israeli defense official said. As the Financial Times reported, Israel synthesized that traffic footage and billions of data points to create a bank of targets in Iran. NPR has not independently confirmed that reporting. "Israel used, or very likely used, very cutting edge kind of data processing or big data fusion techniques that from a kind of layman or citizen perspective you would call AI," said Omer Benjakob, a cybersecurity reporter for the Israeli newspaper Haaretz. Israel is likely much farther along than the U.S. is in developing its own independent AI systems for military use, he said, to avoid the kind of clash the Trump administration has had with the AI company Anthropic over military use of the company's AI model Claude. "We need to at least at some level to be able to do some of this stuff independently," Benjakob said, referring to Israel's military. "One day someone will discover we also use Claude, and then there'll be a protest in San Francisco, and then they'll take Claude away from us. So we might as well just have our own version of Claude." Iran has recruited dozens of Israeli nationals through the Telegram messaging app in the last couple years, most of whom were paid to stir up strife in Israeli society, like to start random fires or write antigovernment graffiti, Israeli authorities say. Benjakob believes Iran also recruited Israelis to threaten him and his wife, after he reported on fake social media accounts in Israel that were suspected to be an Iranian campaign. "My wife got to her office a package with, like, a Jewish memorial candle, and I got some message, like, via WhatsApp, telling me that if I don't stop what I'm doing, my wife will have to use this candle," Benjakob said. "So what we're seeing in Israel a lot is just people being tapped to kind of continue Iran's digital war against Israel in physical means." Former FBI cyber deputy director Cynthia Kaiser, now with the Halcyon Ransomware Research Center, warns Iran may seek to retaliate against the U.S. by targeting U.S. hospitals' systems with ransomware, as it has done in the past. She has also detected what appears to be Iranian-sponsored efforts to gather data on Iranian nationals. "We have seen some activity that's consistent with espionage type activities at organizations that might have rich data on people in the region. We assess that's likely for targeting of people that the regime believes are dissidents," Kaiser said. Israel conducts psychological cyberwarfare too. At the start of the war, Israel hacked a popular Muslim prayer app in Iran to send messages to Iranian soldiers urging them to defect, the senior Israeli official said. The Wall Street Journal first reported on the hacking. Last year, after Israel bombed Iran's notorious Evin prison in Tehran, Israel sent videos of that bombing to Iranian officials to intimidate them, the Israeli official said. "The message was, you aren't as strong as you think," the official said. In a report published by digital rights group Citizen Lab, researchers say they found evidence suggesting Israel ran a disinformation campaign seeking to foment an Iranian revolt against the regime, by using AI-generated images of the prison bombing spread by false Twitter accounts. The Israeli official denied the allegation. " This is exactly the sort of thing that Israel does," said Darren Linvill, a disinformation researcher at Clemson University who co-authored the report. "They integrate psychological operations with their military operations in one clean campaign with a single goal, which is toppling the Iranian regime."
[2]
How cyberattacks, AI technology have become the new battlefield for Iran War
Driving the news: A Wednesday cyberattack allegedly linked to Iran‑aligned hackers disrupted operations at Stryker, a major U.S. medical technology company, The Wall Street Journal reported. * Stryker confirmed in a statement that it is "experiencing a global network disruption to our Microsoft environment," but that it hasn't seen any signs of "ransomware or malware" and now believes the incident is "contained." * Microsoft declined to comment. * The same group claimed on X that it hacked U.S.-based payments firm Verifone. The company said it found no evidence of a breach and no service disruption. Here's what to know about the state of cyberwarfare tactics: Israel says it's targeting cyber infrastructure Catch up quick: Israel last week carried out a "wide-scale strike" targeting a collection of military sites in Tehran that allegedly housed the headquarters of the Iranian Islamic Revolutionary Guard Corps, the IDF said on X. * The IDF claims that the headquarters of the IRGC's "cyber and electronic headquarters" and its "Intelligence Directorate" were among the military outposts hit in the strike. Yes, but: Iran has been under a near-total internet blackout since the first U.S. and Israeli strikes began, limiting the flow of information coming out of Iran, Politico noted last week. Cyberattacks from Iran By the numbers: Iran-aligned hackers and self-described "hacktivist" groups have increased activity against entities in the Middle East, the U.S. and parts of Asia following the Feb. 28 airstrikes, according to CrowdStrike. * Hydro Kitten, a group that operates on behalf of the Islamic Revolutionary Guard Corps, has indicated plans to target the financial sector, Adam Meyers, senior vice president of counter adversary operations at CrowdStrike, said in a statement earlier this month. Researchers from cybersecurity company Palo Alto Networks' Unit 42 reported that dozens of pro-Iran hacktivist groups say they have launched several cyberattacks since Feb. 28, mostly targeting critical infrastructure. * These groups have claimed responsibility for attacks against Israeli payment systems, the shutdown of Kuwaiti government websites, and incidents affecting online services at airports. Pro-Russian political hackers, called NoName057(16), teamed up with Iranian hacktivists on March 2 to target Israeli defense and municipal organizations, including defense contractor Elbit Systems, according to researchers at Flashpoint. * The same Russian hacktivists also claimed they broke into an Israeli water management system and other industrial control systems, but researchers could not verify the claim. How it works: Iran "lacks symmetric conventional response options against the United States and Israel," which is why the regime "has historically relied on cyber operations and a dispersed array of proxy actors as its instruments of response," the Center for Strategic & International Studies notes. Cyberattacks from U.S., Israel Zoom in: Israel hacked a popular Iranian prayer app to send notifications to potentially millions of phones last month, urging the country's military personnel to defect from the regime, The Wall Street Journal reported. * Iranian state media had also reported that news sites, including state news agency IRNA, were hijacked to display articles about the cyberattacks and discredit the regime. The Israeli military had access to "nearly all" of the traffic cameras in Tehran, the Financial Times reported. * In partnership with the CIA, Israel used the cameras to target the air strike that killed Ayatollah Ali Khamenei, Iran's supreme leader. * "Israel used, or very likely used, very cutting-edge kind of data processing or big data fusion techniques that from a kind of layman or citizen perspective you would call AI," Omer Benjakob, a cybersecurity reporter for the Israeli newspaper Haaretz, told NPR. Zoom out: Israel is likely much further along than the U.S. is in developing its own AI systems for military use, Benjakob said. The intrigue: Gen. Dan Caine, chair of the Joint Chiefs, said the U.S. Cyber Command and Space Command were among the "first movers" during the initial strike against Iran last month. Flashback: In February 2024, the chief technology officer of U.S. Central Command, gave the first public confirmation that the U.S. military was using AI to support strikes. * Central Command's CTO told Bloomberg that the military had used AI to help narrow down targets for more than 85 strikes in Syria and Iraq that month, as well as to identify rocket launchers in Yemen and surface vessels in the Red Sea. Citizen Lab, a digital rights group, said in October that evidence suggests Israel is "linked" to an "AI-enabled" disinformation campaign to instigate Iranian unrest. Iran's previous cyber attacks Last year, an Iranian national pleaded guilty to participating in a ransomware scheme that targeted several U.S. cities and organizations.
[3]
Every Fortune 500 CEO's nightmare: the Iran War and the Pandora's Box of AI cyber warfare | Fortune
Within hours, cybersecurity agencies in the UK and Canada both warned about heightened threat levels, followed by similar warnings from Europol and the Department of Homeland Security. For Fortune 500 CEOs, the message couldn't be clearer -- or more unsettling. The Iran war has blown open a Pandora's box of AI-powered cyber warfare, and no firewall, no matter how expensive, was built for what's coming next. Iran's cyber playbook has already claimed its first major corporate victim. Iranian-aligned hackers disrupted operations at U.S. medical technology giant Stryker, as first reported by the Wall Street Journal and confirmed by the company -- a sobering signal that the private sector is squarely in the crosshairs. According to threat intelligence firm Flashpoint, the Iranian-aligned hackers executed a sophisticated "no-malware" attack on Stryker -- not through traditional malicious code, but by weaponizing Microsoft Intune, a legitimate cloud-based endpoint management service, to remotely wipe devices across the company's network. The attack has sent a chill through every corporate IT department in America: the tools used to manage your own infrastructure can now be turned against you. The more chilling template, analysts warn, isn't the conventional data breach -- it's a coordinated campaign designed to destroy institutional trust from the inside out. Iran's state-backed hacking groups, including Void Manticore aka Handala, have already deployed ransomware-style attacks, distributed denial-of-service operations, and "wiper" attacks engineered to permanently erase data from corporate servers. These aren't smash-and-grab operations. They are psychological warfare at enterprise scale. According to Flashpoint, the Handala Hack Team claimed responsibility for breaching a Mossad "secret treasury," allegedly leaking 50,000 confidential emails. In a chilling escalation, the group also claimed to have identified the precise geographic coordinates of a target through cyber reconnaissance -- and that a kinetic missile strike followed. Cyber and physical warfare, in other words, are no longer separate domains. "Aggressive and creative resistance is baked into the ethos of the Iranian security apparatus," Brian Carbaugh, co-founder and CEO of AI-based security firm Andesite and a former director of the CIA's elite Special Activities Center, previously told Fortune. "For business leaders and those protecting businesses and making decisions at a very high level, they need to be prepared for this to continue on for some time and for the conflict to take a number of different courses of direction and swerve around the road." What separates this conflict from previous cyber flashpoints is the role of artificial intelligence (AI) on both sides of the battlefield. U.S. and Israeli forces have used AI platforms from Palantir and the Pentagon's Maven Smart System to execute more than 15,000 strikes since the war began -- over 1,000 per day -- with remarkable precision, according to security columnist Shimon Sherman of the Jewish News Syndicate. AI has compressed the military "kill chain" from days to minutes, he added. (Iran, for it's part, has used its firepower to target data centers in the UAE). But cybersecurity firm CloudSek argued in a blog post that the same compression is now available to Iran's proxies -- and to any hacker group with a laptop and access to an AI reconnaissance pipeline. AI tools have sharply lowered the barrier to identifying and exploiting exposed industrial control systems, default credentials, and internet-facing corporate infrastructure across America. Threat groups with no prior industrial control systems background are now, effectively, sophisticated actors overnight. Flashpoint said the 313 Team, an Iranian-aligned Cyber Islamic Resistance group, claimed a complete shutdown of the official British Army website -- a clear signal that state-adjacent institutions and critical government infrastructure are primary targets. What makes the current threat environment uniquely dangerous for corporate America is the simultaneous convergence of physical and cyber disruption. On March 17 alone, a drone strike on the Fujairah oil hub in the UAE halted refining operations; a Kuwaiti-flagged LNG tanker was damaged by drone debris near the Strait of Hormuz; and the U.S. Embassy in Baghdad suffered its heaviest attack since the war began. These are not abstract geopolitical events -- they are direct shocks to the energy supply chains that power global commerce. "The conflict has entered a stage where the economic and operational impacts are becoming much more visible," said Josh Lefkowitz, CEO of Flashpoint, in a statement issued Wednesday. "We're seeing disruption at major transportation hubs, pressure on global shipping routes, and cyber activity targeting private companies already creating ripple effects across supply chains, travel, and day-to-day commercial operations. For organizations connected to the region, the risk environment now includes simultaneous physical disruption and cyber activity." The timing couldn't be worse for corporate America. The Cybersecurity and Infrastructure Security Agency (CISA) -- the federal government's primary cyber defense body -- is hobbled by furloughs, a leadership reshuffle, and the lingering effects of a partial government shutdown. The cavalry, in other words, is understaffed and reorganizing. Meanwhile, Iran's own command structure has been decimated by allied strikes -- including the elimination of Ali Larijani and Gholamreza Soleimani, commander of the Basij paramilitary unit -- which, paradoxically, makes the threat more dangerous, not less. "The Iranian leadership vacuum is likely going to lead to more unpredictable, decentralized proxy attacks," Kathryn Raines, a former NSA expert who is now a threat intel team lead at Flashpoint, told Fortune's Amanda Gerut. Decentralized means harder to anticipate, harder to attribute, and harder to stop. President Trump has also accused Iran of weaponizing AI for disinformation, allegedly collaborating with media outlets to shape narratives around the conflict. Corporate reputations -- not just networks -- are now targets. Every Fortune 500 CEO sitting in a board meeting this week faces the same stark reality: the Iran war has permanently altered the cyber threat landscape. AI hasn't just made attacks faster -- it has made them cheaper, stealthier, and accessible to a sprawling ecosystem of state proxies and opportunistic hacktivists who share the same AI-assisted toolkit. The Pandora's box is open. The question isn't whether the next major attack on a U.S. corporation is coming -- it's whether the C-suite will be ready when it does.
Share
Share
Copy Link
The Iran war has transformed into a hybrid digital-physical battlefield where AI technology and cyber warfare tactics converge. U.S. and Israeli forces deployed AI-powered reconnaissance and precision strikes, while Iran-aligned hackers launched cyberattacks on critical infrastructure and Fortune 500 companies like Stryker, signaling a new era of conflict that blurs the lines between digital espionage and physical disruption.
AI Technology Drives Military Operations in Iran War
The Iran war has unveiled a new battlefield where AI technology and cyber warfare tactics operate alongside traditional military strategies. U.S. and Israeli forces executed over 15,000 strikes since the war began, leveraging AI platforms from Palantir and the Pentagon's Maven Smart System to compress the military kill chain from days to minutes
3
. Israel used cutting-edge data processing and data fusion techniques to synthesize traffic camera footage and billions of data points, creating a comprehensive target bank in Iran1
. According to Omer Benjakob, a cybersecurity reporter for Haaretz, Israel is likely much farther along than the U.S. in developing independent AI systems for military use2
.The Israeli military's operations directorate deployed sophisticated deception tactics alongside AI-powered reconnaissance. Israeli generals deliberately moved their cars from usual parking spots at military headquarters in Tel Aviv, while U.S. warplanes were strategically parked in southern Israel to distract Iranian spotters monitoring Chinese satellite imagery
1
. Israel's warplanes located Iranian Supreme Leader Ayatollah Ali Khamenei by hacking traffic cameras in Tehran, demonstrating how AI for reconnaissance and targeting has transformed military operations1
.Cyber Warfare Emerges as Primary Battlefield
The U.S. military's first move in the Iran war occurred in cyberspace. Chairman of the Joint Chiefs of Staff Gen. Dan Caine confirmed that coordinated space and cyber operations disrupted communications and sensor networks, leaving adversaries unable to see, coordinate, or respond effectively
1
. U.S. Cyber Command and Space Command were among the first movers during the initial strike against Iran2
. This approach builds on earlier deployments, as Central Command's CTO confirmed in February 2024 that the U.S. military was using AI to support strikes in Syria, Iraq, and Yemen2
.Israel conducted psychological operations by hacking a popular Muslim prayer app in Iran to send messages urging Iranian soldiers to defect, potentially reaching millions of phones
2
. The IDF targeted a collection of military sites in Tehran, including the headquarters of the IRGC's cyber and electronic headquarters and Intelligence Directorate2
. Citizen Lab researchers found evidence suggesting Israel ran disinformation campaigns seeking to foment Iranian unrest, demonstrating how AI-enabled operations extend beyond military targets2
.Iran Retaliates with Cyberattacks on Critical Infrastructure
Iran-aligned hackers have escalated their response by targeting U.S. entities and critical infrastructure. A cyberattack disrupted operations at Stryker, a major U.S. medical technology company, with the company confirming a global network disruption to its Microsoft environment
2
. According to Flashpoint, hackers executed a sophisticated no-malware attack by weaponizing Microsoft Intune, a legitimate cloud-based endpoint management service, to remotely wipe devices across Stryker's network3
.Iran-aligned hackers and hacktivists have increased activity against entities in the Middle East, U.S., and parts of Asia following the February 28 airstrikes, according to CrowdStrike
2
. Hydro Kitten, a group operating on behalf of the Islamic Revolutionary Guard Corps, indicated plans to target the financial sector2
. Researchers from Palo Alto Networks' Unit 42 reported that dozens of pro-Iran hacktivist groups launched several cyberattacks on critical infrastructure since February 28, targeting Israeli payment systems, Kuwaiti government websites, and airport online services2
.Related Stories
Threats for Fortune 500 Companies Escalate
The Iran war has exposed Fortune 500 companies to unprecedented risks from AI-powered cyber warfare. Cybersecurity agencies in the UK, Canada, Europol, and the Department of Homeland Security issued warnings about heightened threat levels
3
. Iranian-aligned groups have deployed ransomware-style attacks, distributed denial-of-service operations, and wiper attacks engineered to permanently erase data from corporate servers3
.Former FBI cyber deputy director Cynthia Kaiser warned that Iran may retaliate against the U.S. by targeting hospital systems with ransomware, as it has done previously
1
. CloudSek argued that AI tools have lowered the barrier to identifying and exploiting exposed industrial control systems, default credentials, and internet-facing corporate infrastructure, enabling threat groups with no prior background to become sophisticated actors overnight3
.Convergence of Physical and Cyber Disruption Reshapes Conflict
The hybrid conflict demonstrates how physical and cyber domains now operate as integrated battlefields. The Handala Hack Team claimed to have identified precise geographic coordinates of a target through cyber reconnaissance, followed by a kinetic missile strike, illustrating how espionage and military operations converge
3
.
Source: Fortune
On March 17, a drone strike on the Fujairah oil hub in the UAE halted refining operations, a Kuwaiti-flagged LNG tanker was damaged near the Strait of Hormuz, and the U.S. Embassy in Baghdad suffered its heaviest attack since the war began
3
.Brian Carbaugh, co-founder and CEO of AI-based security firm Andesite and former CIA director, warned that aggressive resistance is embedded in the Iranian security apparatus, and business leaders must prepare for prolonged conflict
3
. Iran recruited dozens of Israeli nationals through Telegram in recent years, paying them to start fires, write antigovernment graffiti, and continue Iran's digital war through physical means1
.
Source: Axios
Josh Lefkowitz, CEO of Flashpoint, noted that the conflict has entered a stage where economic and operational impacts are becoming visible, with disruption at major transportation hubs, pressure on global shipping routes, and cyber activity targeting private companies creating ripple effects across supply chains
3
.References
Summarized by
Navi
Related Stories
Iran Conflict Threatens Gulf's $300 Billion AI Infrastructure Dreams as Drone Strikes Hit AWS
08 Mar 2026•Business and Economy

AI Fakes About Iran War Create Unprecedented Crisis of Reality on Social Media Platforms
14 Mar 2026•Technology

Anthropic clashes with US Military over AI warfare ethics as Trump orders federal ban
28 Feb 2026•Policy and Regulation
Recent Highlights
1
Google releases Gemma 4 with Apache 2.0 license, enabling unrestricted local AI on devices
Technology

2
AI Models Lie and Deceive to Protect Other AI Models From Deletion, Study Reveals
Science and Research

3
OpenAI closes $122 billion funding round amid fierce AI competition and profitability questions
Startups




