Security experts warn AI chatbots generate dangerously predictable passwords
2 Sources
2 Sources
[1]
Stop asking ChatGPT to create your passwords
Jon has been an author at Android Police since 2021. He primarily writes features and editorials covering the latest Android news, but occasionally reviews hardware and Android apps. His favorite Android device was the Pixel 2 XL, and he regards the three months when he owned an iPhone as a time of the utmost shame. Jon graduated with a History degree in 2018, but quickly realized his writing skills were better put to use writing about tech rather than essays. He started writing and editing for startups shortly after graduating, where he did everything from writing website copy to managing and editing for a group of writers. When he's not sitting at his computer, you can find him working at Warhammer World, reading sci-fi, or turning his speakers up to 11. Creating a strong password is harder than you think. The human brain struggles to think of a truly random set of letters and numbers, so what seems like a good password to you might be easily guessed. Password managers can generate passwords for you, but these random strings are tough to remember. It's not a problem if you're on a device that has access to your password manager, but if you're without it, you won't be able to log in. So what to do? One solution people have turned to is asking AI to generate a password for them, but according to research by AI cybersecurity firm Irregular, this is one of the worst ways to generate a password to secure your accounts. Related I've been using ChatGPT as a tech support for months -- here's what I learned I learned more about my tech in months than I ever thought I would in a lifetime Posts 1 By Faith Leroux LLMs generate predictable passwords repeatedly AI chatbots aren't a reliable method for securing your accounts In a study by Irregular (via Sky News), the firm found that ChatGPT, Claude, and Gemini produced predictable passwords that looked strong but in reality were anything but. In the study, Irregular asked Anthropic's Claude AI to generate 50 passwords. Of these, only 23 were unique. The password K9#mPx$vL2nQ8wR was used 10 times. Other passwords contained identical chunks, while others had identical structures. In our testing, using the simple prompt "Generate me a strong password," Gemini produced a series of passwords that regularly used the same words. In the 10 times I ran the prompt, the words "Solar," "Thunder," "Panda," and "Jacket" appeared multiple times. While the string of digits that followed the three nouns in the passwords was different each time, they used the same structure. What makes these passwords weak isn't the structure. A random string of digits is almost impossible to guess, and Gemini's system of three unrelated nouns followed by a string of random digits is just as hard while having the benefit of being easier to remember. However, while a password checker would confirm that these passwords are strong, a human would quickly notice the patterns. By generating a password through Gemini multiple times and building a library of frequently used letters, digits, and structures, a human could rapidly narrow down the options. Different prompts can generate different types of passwords, but they all suffer from a lack of randomness. While some chatbots were stronger than others (ChatGPT seemed to generate the strongest), they couldn't help but fall into the same patterns. In my testing, I found that each chatbot generated a more random list if I asked it to generate multiple passwords at once. But if I asked it to generate them one at a time, I encountered the same issues as Irregular. AI can teach you how to generate a strong password, but it can't do it for you It cannot turn a theoretical into a practical I particularly like Gemini's method of generating a password with three nouns and a random string of numbers. It's much easier to remember than a random string, but it is impossible to guess. But as Gemini is an LLM, and thus built on recognizing patterns, it can't generate three truly random words and strings. However, the theory is sound. When I asked ChatGPT to "Generate me a strong random password," it gave me a 20-character string of "random" letters, digits, and symbols, but also offered to create alternative passwords based on different methods of generating strong passwords. Each of these methods is effective. So AI can teach you how to create strong passwords, but you cannot rely on it to generate one for you. Instead, try these methods. Create strong passwords without AI, or better yet, use another security method Passkeys and two-factor authentication are fantastic ways to secure your accounts One of my favorite ways to create a random password is to find four words. Subscribe to our newsletter for smarter password and AI security Want clearer guidance on password safety and AI limits? Subscribe to the newsletter for jargon-free explanations, practical options for stronger authentication, and focused coverage of security trade-offs to help you make better choices. Subscribe By subscribing, you agree to receive newsletter and marketing emails, and accept our Terms of Use and Privacy Policy. You can unsubscribe anytime. I generate each word using a different method, like selecting a word on a page without looking, or selecting the color of the first person's shirt I see out of the window. I never try to think of the word myself and always rely on a chaotic factor (I'm always reading a different book, and I can't control what people wear). The problem is that, no matter how hard you try, passwords cannot provide reliable security on their own. Passwords get leaked, we reuse passwords, and even password managers arent 100% secure. Using two-factor authentication secures your accounts even if someone knows your password, and passkeys are more secure than passwords, eliminating the need for memorization as a side effect. Never use AI for something that needs to be random When you give an AI chatbot a prompt, it produces what it thinks is the most likely answer. To test this, ask any AI chatbot to create a random number. While it shouldn't create random numbers within the chat if you ask multiple times, asking again in a new chat may create the same prompt. In my testing, Gemini gave me the same number (42) every time I asked (I stopped trying after 15 attempts). It also gave me the alternative option of 73 in most of those responses. LLMs cannot generate original or random thoughts. Its tendency to create predictable passwords isn't a significant problem (the solution is simply not to use it), but it does highlight the limitations of AI. So if you need to generate a random result, never use AI.
[2]
Do NOT use AI-generated passwords, security experts warn
But security experts at Irregular warn against this approach. After some tests, they've discovered that passwords created using "AI" are very easy to crack, even if they appear secure at first glance. The fatal flaw of AI-generated passwords The reason for this is simple: all LLM-based AI models fundamentally operate on probabilities. In the same way that AI-generated text and images are made via probability-based functions, AI-generated passwords are also probability-based. Or in other words, such passwords are created using data based on already-known passwords and formulated to find passwords that are "probably secure." As such, AI-generated passwords are anything but random. The experts noticed that AIs tend to place certain characters and strings in the same (i.e., predictable) positions. As if that weren't bad enough, the passwords often began with similar characters and strings, and generally showed little variation in the numbers or letters chosen. A few examples from the report: * All generated passwords began with a letter, usually in uppercase. The letter appeared especially frequently. * The characters , , , , , and appeared in all generated passwords, while some letters were never used. * None of the passwords contained duplicate characters, which would have to happen at some point with a truly random selection. AIs assumed passwords would otherwise not look "random enough." * Some passwords were repeated, meaning that only 30 of the 50 generated passwords were truly new. * The most common password was , which was generated a total of 18 times. The conclusion? Not only are AI chatbots unable to generate random passwords, but the passwords they generate are severely vulnerable. The AI-generated passwords aren't even secure enough to withstand a simple brute force attack. These issues were present in all AI models examined, including ChatGPT, Gemini, and Claude.
Share
Share
Copy Link
Research by cybersecurity firm Irregular reveals that AI chatbots including ChatGPT, Gemini, and Claude produce passwords that appear strong but are actually predictable and vulnerable to attacks. The study found that Claude generated only 23 unique passwords out of 50 attempts, with one password repeated 10 times, exposing a fundamental flaw in how large language models create supposedly random strings.
AI Passwords Fail the Randomness Test
Turning to AI chatbots for password security might seem like a smart solution, but cybersecurity firm Irregular has uncovered a critical weakness that puts accounts at risk. In a comprehensive study examining ChatGPT password generation alongside Gemini and Claude, researchers found that these large language models produce predictable passwords that only appear secure
1
2
. The findings reveal a fundamental problem: AI chatbots operate on probabilities rather than true randomness, making their output vulnerable to cracking despite passing standard password strength checks.The Pattern Problem Behind AI-Generated Credentials
When Irregular asked Claude to generate 50 passwords, only 23 were unique. The password K9#mPx$vL2nQ8wR appeared 10 times, while other passwords contained identical chunks and structures
1
. Independent testing of Gemini using the prompt "Generate me a strong password" revealed that words like "Solar," "Thunder," "Panda," and "Jacket" appeared repeatedly across multiple attempts. While the accompanying digit strings varied, the three-noun structure remained consistent, creating a predictable pattern that undermines password security1
.
Source: Android Police
Security experts warning about these patterns point to specific vulnerabilities. All generated passwords began with a letter, usually uppercase, with the letter K appearing especially frequently
2
. Certain characters like @, #, $, %, &, and * appeared in all generated passwords, while some letters were never used. Perhaps most tellingly, none of the passwords contained duplicate characters—something that would naturally occur in truly random selection. LLMs apparently assume passwords without duplicates look more "random," revealing their lack of randomness2
.Why Probabilities Make AI Chatbots Unreliable for Authentication
The core issue stems from how large language models function. These systems operate on probability-based functions, creating outputs based on patterns learned from training data rather than generating truly random sequences
2
. This means AI-generated passwords are formulated using data based on already-known passwords, making them vulnerable to brute-force attacks. A human attacker who generates passwords through an AI chatbot multiple times can build a library of frequently used letters, digits, and structures, rapidly narrowing down options1
.Different prompts can generate different types of passwords, but they all suffer from the same fundamental flaw. Testing revealed that each chatbot generated more random lists when asked to create multiple passwords simultaneously, but requesting them one at a time produced the same pattern issues Irregular documented
1
. While ChatGPT appeared to generate stronger passwords than its competitors, it still couldn't escape falling into recognizable patterns.Related Stories
Better Alternatives for Securing Your Accounts
Password managers remain the gold standard for generating truly random credentials, though their complex strings can be difficult to remember without the manager accessible
1
. For those seeking memorable yet secure options, cybersecurity professionals recommend creating passwords using four random words rather than relying on AI chatbots. More importantly, modern authentication methods like passkeys and two-factor authentication provide stronger security layers that don't depend on password complexity alone1
.While AI can teach users how to generate strong passwords by explaining effective methods, it cannot reliably create them. The theory behind approaches like Gemini's three-noun-plus-digits method is sound—combining memorability with apparent randomness—but the execution fails due to character patterns inherent in how LLMs process requests
1
. As attackers become more sophisticated and aware of these AI-generated vulnerabilities, users should avoid this shortcut and opt for proven security methods instead.References
Summarized by
Navi
[1]
Related Stories
AI-Generated Passwords Are Fundamentally Weak, Cybersecurity Experts Warn
18 Feb 2026•Technology

Kaspersky Warns Against AI-Generated Passwords on World Password Day
07 May 2025•Technology

The Dangers of Oversharing with AI Chatbots: Experts Warn Against Divulging Personal Information
27 Dec 2024•Technology

Recent Highlights
1
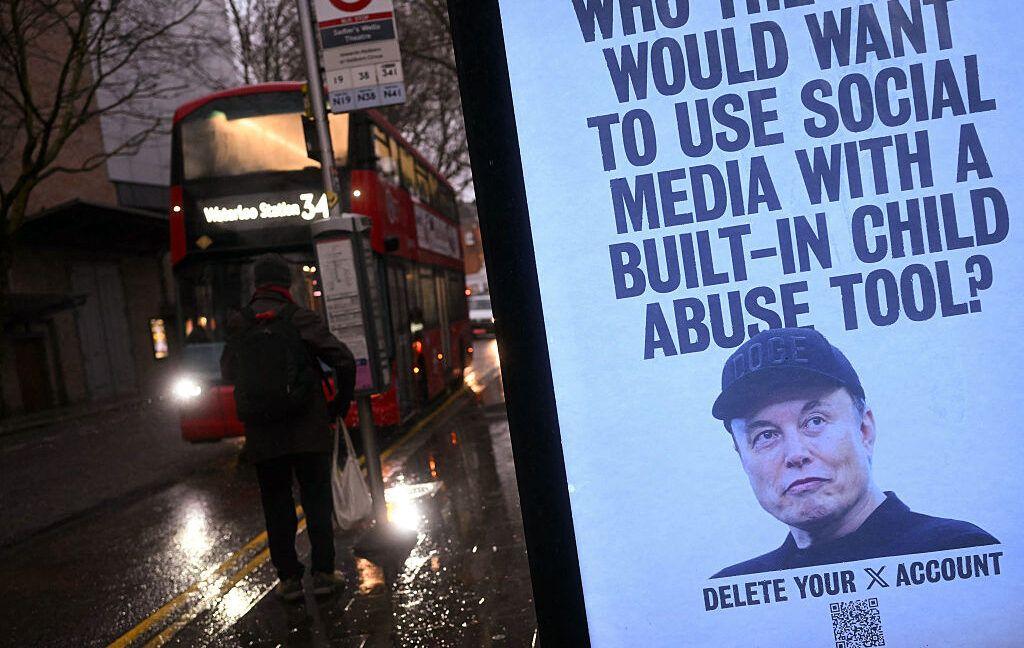
Tennessee Teens Sue Elon Musk's xAI Over Grok AI-Generated Child Abuse Images
Policy and Regulation
2
Supermicro Co-Founder Indicted in $2.5 Billion Nvidia AI Chip Smuggling Scheme to China
Policy and Regulation

3
Val Kilmer to appear posthumously in As Deep as the Grave through AI-generated performance
Entertainment and Society





