North Korean Hackers Use AI Social Engineering in $100,000 Crypto Attack on Zerion
2 Sources
[1]
North Korea Used AI to Hack Zerion in Second Crypto Attack
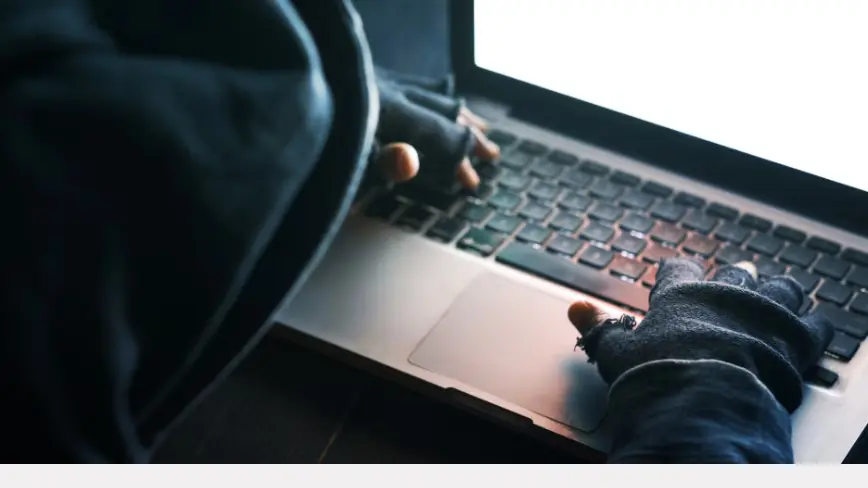
It is the second long-term social-engineering attack this month, after the $280 million exploit of the Drift Protocol. Crypto wallet Zerion revealed that North Korean-affiliated hackers used AI in a long-term social engineering attack to steal about $100,000 from the company's hot wallets last week. The Zerion team released a post-mortem on Wednesday, where it confirmed that no user funds, Zerion apps or infrastructure were affected and that it had proactively disabled the web app as a precaution. While the amount was relatively small in crypto hacking terms, it is another incident of a crypto worker being targeted for an "AI-enabled social engineering attack linked to a DPRK threat actor," Zerion said. It is the second attack of this nature this month, following the $280 million exploit of the Drift Protocol, which was the victim of a "structured intelligence operation" by DPRK-affiliated hackers. The human layer, not smart contract bugs, has now become North Korea's primary point of entry into crypto firms. Zerion said the attacker gained access to some team members' logged-in sessions and credentials, as well as private keys to company hot wallets. "This incident showed that AI is changing the way cyber threats work," the company said. It confirmed that the attack was similar to those that had been investigated by the Security Alliance (SEAL) last week. Related: Researchers discover malicious AI agent routers that can steal crypto SEAL reported that it had tracked and blocked 164 domains linked to the DPRK group UNC1069 in a two-month window from February to April. It stated that the group operates "multiweek, low-pressure social engineering campaigns" across Telegram, LinkedIn and Slack. Malicious actors impersonate known contacts or credible brands or leverage access to previously compromised company and individual accounts. "UNC1069's social engineering methodology is defined by patience, precision, and the deliberate weaponization of existing trust relationships." Google's cybersecurity unit Mandiant detailed in February the group's use of fake Zoom meetings and a "known use of AI tools by the threat actor for editing images or videos during the social engineering stage." Earlier this month, MetaMask developer and security researcher Taylor Monahan said North Korean IT workers have been embedding themselves in crypto companies and decentralized finance projects for at least seven years. "The evolution of the DPRK's social engineering techniques, combined with the increasing availability of AI to refine and perfect these methods, means the threat extends well beyond exchanges," blockchain security firm Elliptic said in a blog post earlier this year. "Individual developers, project contributors, and anyone with access to cryptoasset infrastructure is a potential target."
[2]
Zerion Links Crypto Attack to North Korean Hackers Using AI Tactics
Zerion plans stronger authentication and security training The Zerion team released a post-mortem report on Wednesday, claiming that North Korean-affiliated hackers were using AI-enabled social engineering in a cyberattack. Hackers stole around $100,000 (roughly Rs. 93.4 lakh) from the company's hot wallets last week. It was later confirmed that no user funds, Zerion apps or infrastructure were affected and that the company had disabled the web app as a precautionary move. Zerion further added that the attacker gained access to some team members' logged-in sessions and credentials, as well as private keys to company hot wallets. Report Highlights Growing Use of AI in Cyberattacks The firm stated that the attack was similar to those that had been investigated by the Security Alliance last week. Between February and April, the nonprofit Security Alliance (SEAL) reported that it had tracked and blocked over 164 domains linked to the DPRK group UNC1069. It was also mentioned in the report that the group operates "multiweek, low-pressure social engineering campaigns" across Telegram, LinkedIn and Slack. Malicious people impersonate trusted brands or known contacts, or they use access to company and individual accounts that have already been hacked. In a post on X, Zerion addressed this issue and gave a glimpse of how the road looked ahead. The crypto wallet said, "This incident showed that AI is changing the way cyber threats work. We are taking steps to further strengthen Zerion's security," The firm added in the post that they will be strengthening internal policies for using credentials and authentication. The Web app will be restored in the next 48 hours. The team will be investing in team security training and working to accelerate security compliance. Last week, security researcher Taylor Manonan claimed that North Korean IT workers have been infiltrating DeFi platforms for the past 7 years. This includes the Drift Protocol hack as well, which disclosed a $280 million (roughly Rs. 2,600 crore) exploit, which also had a DPRK group behind it. Drift Protocol explained that this was not a typical hack, but a months-long, highly coordinated social engineering operation. In a blog post earlier this year, blockchain security firm Elliptic also stated that "The evolution of the DPRK's social engineering techniques, combined with the increasing availability of AI to refine and perfect these methods, means the threat extends well beyond exchanges." This incident reflects how cyber threats in the crypto ecosystem are evolving with the help of AI, which are making attacks more targeted and harder to detect. Cases like Zerion wallet and Drift protocol serve as an example that even established platforms are not immune to cyber threats, and hence, it reinforces the need for stringent security across the crypto landscape.
Share
Copy Link
North Korean-affiliated hackers used AI social engineering to steal $100,000 from crypto wallet company Zerion's hot wallets. The attack marks the second major DPRK-linked breach this month, following Drift Protocol's $280 million exploit. Security experts warn that AI-driven threats are making attacks more sophisticated and harder to detect.
North Korean Hackers Deploy AI-Enabled Social Engineering Attacks
Crypto wallet company Zerion became the latest victim of a sophisticated crypto attack orchestrated by North Korean hackers who leveraged artificial intelligence to execute a long-term social engineering operation. The breach, which resulted in approximately $100,000 stolen from the company's hot wallets last week, represents a troubling evolution in cyber threats targeting the cryptocurrency industry
1
.
Source: Cointelegraph
In a post-mortem report released Wednesday, Zerion confirmed that attackers gained access to team members' logged-in sessions, credentials, and private keys to company hot wallets. While the stolen amount was relatively modest by crypto standards, the company emphasized that no user funds, Zerion apps, or infrastructure were compromised. As a precautionary measure, the web app was proactively disabled but is expected to be restored within 48 hours
2
.
Source: Gadgets 360
Second Major DPRK-Linked Breach This Month
This incident marks the second AI social engineering attack linked to a DPRK threat actor this month. Earlier, Drift Protocol suffered a devastating $280 million exploit through what investigators described as a "structured intelligence operation" by DPRK-affiliated hackers. The pattern reveals a critical shift in cyber threats: North Korean operatives are now primarily targeting cryptocurrency firms through human vulnerabilities rather than exploiting smart contract bugs
1
."This incident showed that AI is changing the way cyber threats work," Zerion stated in their analysis. The company confirmed similarities between their breach and attacks investigated by the nonprofit Security Alliance (SEAL) last week
2
.Tracking the UNC1069 Group's Sophisticated Campaigns
Security Alliance reported tracking and blocking 164 domains linked to the DPRK group UNC1069 during a two-month window from February to April. The group operates "multiweek, low-pressure social engineering campaigns" across platforms including Telegram, LinkedIn, and Slack. Malicious actors succeed by impersonating contacts, leveraging credible brand identities, or exploiting access to previously compromised company and individual accounts
1
.According to SEAL's findings, "UNC1069's social engineering methodology is defined by patience, precision, and the deliberate weaponization of existing trust relationships." This approach allows attackers to build credibility over extended periods before executing their cyberattack
1
.Related Stories
AI-Driven Threats Reshape the Security Landscape
Google's cybersecurity unit Mandiant detailed in February the group's use of fake Zoom meetings and confirmed use of AI tools for editing images or videos during the social engineering stage. This technological enhancement makes AI-driven threats increasingly difficult to detect and defend against. MetaMask developer and security researcher Taylor Monahan revealed earlier this month that North Korean IT workers have been embedding themselves in crypto companies and decentralized finance projects for at least seven years
1
.Blockchain security firm Elliptic warned that "the evolution of the DPRK's social engineering techniques, combined with the increasing availability of AI to refine and perfect these methods, means the threat extends well beyond exchanges. Individual developers, project contributors, and anyone with access to cryptoasset infrastructure is a potential target"
1
.Strengthening Defenses Against Evolving Threats
In response to the breach, Zerion announced comprehensive security enhancements. The company plans to strengthen internal policies for using credentials and authentication, invest in team security training, and accelerate security compliance initiatives. These measures reflect industry recognition that traditional security protocols must adapt to counter AI-enabled social engineering attacks
2
.The incidents at both Zerion and Drift Protocol demonstrate that even established platforms remain vulnerable to sophisticated attacks that target cryptocurrency firms through human-focused tactics. As AI tools become more accessible and refined, security experts anticipate that these attacks will grow more targeted and harder to detect, requiring constant vigilance and updated security protocols across the entire crypto ecosystem.
References
Summarized by
Navi
[1]
Related Stories
North Korea-Linked UNC1069 Uses AI-Powered Attacks to Target Cryptocurrency Organizations
10 Feb 2026•Technology

AI-powered crypto hacks drain $600M from DeFi as North Korean state actors exploit vulnerabilities
15 May 2026•Technology
North Korean Hackers Intensify Efforts to Infiltrate Crypto Industry
14 Aug 2025•Technology

Recent Highlights
1
Anthropic raises $65 billion, overtakes OpenAI as most valuable AI startup at $965 billion valuation
Business and Economy
2
Apple's Siri overhaul for iOS 27 brings Gemini integration and standalone app to compete with ChatGPT
Technology

3
Google AI Search officially replaces traditional web search with Gemini-powered conversations
Technology