Anthropic launches Claude Security to scan code for flaws and prioritize fixes for enterprises
6 Sources
[1]
Anthropic's new Claude Security tool scans your codebase for flaws - and helps you decide what to fix first
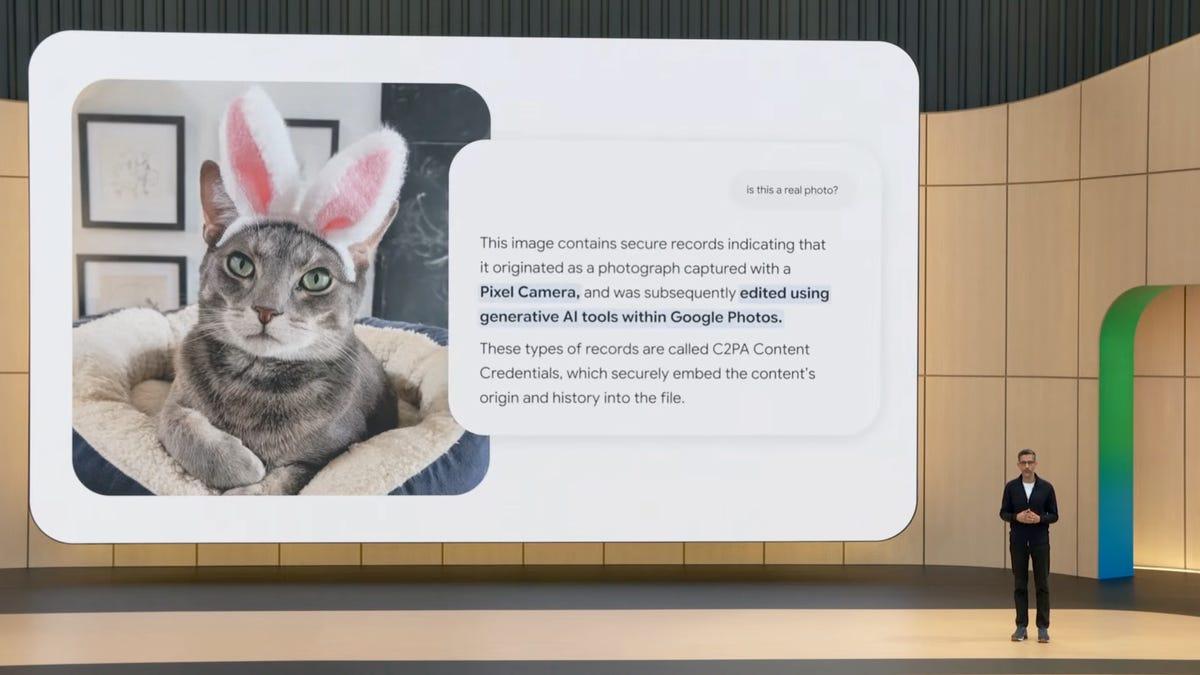
Claude Security turns findings into prioritized fix guidance. Anthropic has announced Claude Security, a new defensive cybersecurity product. Right now, it's available in public beta to Enterprise-tier Claude users, with availability "coming soon" to Claude Team and Max-tier users. Also: Apple, Google, and Microsoft join Anthropic's Project Glasswing to defend world's most critical software Claude Security is another tool in Anthropic's cyberdefense toolbox. It gives security teams a way to "scan codebases for vulnerabilities and generate targeted patches" using the Claude Opus 4.7 model. Earlier in the month, Anthropic debuted Project Glasswing, an AI Manhattan Project aimed at finding vulnerabilities in the world's infrastructure of open-source software. Glasswing uses an Anthropic model called Mythos, a model deemed so dangerous that it's not being released to the public. It's being shared with Glasswing participants, including erstwhile competitors like Amazon Web Services, Anthropic, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, the Linux Foundation, Microsoft, Nvidia, and Palo Alto Networks. At the core of both Project Glasswing and Claude Security is vulnerability scanning. Most cyberattacks begin with an enemy actor exploiting a vulnerability. So, if defenders can find and patch the vulnerabilities, the malicious perpetrator has a smaller attack surface. Remember Star Wars? The entire plot of A New Hope revolves around Death Star plans that Princess Leia stores in R2-D2. Once the Rebels get those plans, they're able to find a vulnerability. All Luke and the other pilots have to do is fire one torpedo down an exhaust port on the Death Star, and... boom! That, boys and girls, is a vulnerability. The Death Star had one fatal flaw. Your codebase probably has more. Anthropic's new Claude Security tool wants to find them before attackers get there first. Back in the real world, everything runs on software, which is inherently vulnerable. Not only do vulnerabilities open doors for adversaries to exploit, but they also could cause damage simply by existing and causing bugs experienced by users of the software. Also: I teamed up two AI tools to solve a major bug - but they couldn't do it without me I first used AI to do vulnerability scanning back in September with OpenAI's Codex. At the time, it failed because it couldn't handle a project-wide context. But when I teamed the AI pair programming tool with ChatGPT's Deep Research, which was better with lots of data, the two found a number of critical vulnerabilities in my security software, which I immediately fixed. Since then, both Codex and Claude Code have got better in terms of how much code they can process in one context, but neither is capable of handling an entire large codebase at once. Mythos can, however. It can even handle the relationships between codebases on a macro scale. But it's not available to the public, even via Enterprise-tier fees. Last month, OpenAI introduced Codex Security, which also offers a larger-scope context analysis. And now Claude Security can do similar larger-scale scans. This new product is capable of scanning a full repository or a targeted directory. According to Anthropic, "Claude reasons about code the way a security researcher does, tracing data flows, reading source code, and working out how components interact across files and modules." There's more to Claude Security, but first let's talk about the big vulnerability introduced by vulnerability-scanning AIs. Vulnerability scanners help defenders defend. But they also help attackers find where to attack. That was the whole point with the Rebels' attack on the Death Star. Once they knew of a vulnerability, they could exploit it. For example, both Microsoft and OpenAI have reported that state-affiliated actors from China, Iran, Russia, and North Korea have used large language models to research various companies and cybersecurity tools, debug code, generate scripts, and create content likely for use in phishing and spear-phishing campaigns. Also: AI is getting scary good at finding hidden software bugs - even in decades-old code Anthropic is trying to prevent its models from being used in similar ways. As of the launch of Opus 4.7, the company includes new cyber safeguards that automatically detect and block requests suggestive of prohibited or high-risk cybersecurity uses. For example, Opus 4.7 now blocks "Activities that are almost always used maliciously and have little to no legitimate defensive application such as mass data exfiltration or ransomware code development." On the other hand, what about activities that have legitimate defensive applications, such as vulnerability exploitation or offensive security tooling development? Opus 4.7 also blocks these activities, but cybersecurity researchers who are approved to join Anthropic's Cyber Verification Program gain access to AI capabilities in this restricted gray zone. Also: This new Claude Code Review tool uses AI agents to check your pull requests for bugs - here's how Effectively, those able to obtain a security clearance from Anthropic can use Opus 4.7 to perform blocked security activities in the course of doing their job. Disclosure: I am an authorized member of Anthropic's Cyber Verification Program, so I have access to these capabilities as part of my cyberwarfare, cyberdefense, and counterterrorism work. The problem with vulnerability scanning is that it can become a firehose of noise. Every little thing can be flagged, and you can spend hours or days chasing down a bug that is of fairly little consequence instead of repairing a vulnerability that can cause an extinction-level event. Claude Security is introducing a "multi-stage validation pipeline independently verifies each finding before it reaches an analyst, and every result gets a confidence rating." The AI is able to explain each "finding" in detail, including factors like confidence, severity, likely impact, reproduction steps, and recommended fix. This can be enormously helpful, because developers can then prioritize working on those high-confidence, large-impact, severely troubling problems first, without having to waste time on lesser issues. Also: Why AI is both a curse and a blessing to open-source software - according to developers From these findings, Claude Security gives defenders the ability to open the code in Claude Code, in context, so they can see and modify the areas needing work right from the finding results. Anthropic has also added a series of workflow optimizations. It says, "We've added scheduled scans for ongoing coverage, the ability to dismiss findings with documented reasons (so future reviewers can trust prior triage decisions), and CSV and Markdown export for integrating findings into existing tracking and audit systems." Claude Security subscribers can work with technology and security partners. Anthropic specifically pointed out technology partners including CrowdStrike, Palo Alto Networks, SentinelOne, Trend.ai, and Wiz, which are integrating Opus 4.7 into their cybersecurity platforms. Also: Google bets $32B on AI agent cyber force as security arms race escalates The company is also working with security partners including Accenture, BCG, Deloitte, Infosys, and PwC, which are deploying Claude Security to help enterprises strengthen their security posture. Do you see AI vulnerability scanning as more useful for finding dangerous flaws or for helping developers prioritize fixes faster? Let us know in the comments below.
[2]
Anthropic announces Claude Security public beta to find and fix software vulnerabilities - SiliconANGLE
Anthropic announces Claude Security public beta to find and fix software vulnerabilities Anthropic PBC announced the launch of Claude Security in public beta mode today to help cybersecurity teams scan their codebases for vulnerabilities and generate patches. Part of Claude Enterprise, the company's subscription model aimed at large organizations, Security began as a research preview as Claude Code Security in February. Since its introduction, the company said hundreds of organizations have used it to discover and fix exploits in production code, including vulnerabilities existing tools had missed for years. The new security tool is powered by the company's flagship artificial intelligence model, Opus 4.7, as a dedicated defensive product, part of a longer-term trend for the company as a cybersecurity angle. Anthropic recently launched Project Glasswing, debuting the use of the company's Mythos model, which was not originally designed as a security model but has proved particularly adept at discovering vulnerabilities. Glasswing brings together numerous technology partners to secure the world's production software. Following this initiative, the company said customers can now work with partners building on Claude's security capabilities. This includes Anthropic's technology partners, such as CrowdStrike Holdings Inc., Palo Alto Networks Inc., SentinelOne Inc., Trend Micro Inc.'s Trend.ai and Wiz Inc., integrating Opus 4.7 into their cybersecurity platforms. Anthropic said that with these new capabilities, Claude can now reason over entire codebases by thinking similarly to the way a cybersecurity researcher does. Instead of looking for known patterns, it traces data flows, reads source code and examines interactions between code components and files to synthesize network effects. The model then verifies everything with a confidence rating before it reaches an analyst so that it can provide more trustworthy outputs. Anthropic also said the model will do its homework as it goes, explaining its reasoning along the way, its confidence factors, the likelihood that a vulnerability can be exploited, the triage factors and how effective a fix will be. From there, users can open a Claude Code session to apply the fix directly in context, with no more waiting days to go back and forth with security and engineering teams to get it tested and working. Anthropic said that after feedback from the research preview, the company added scheduled scans for ongoing coverage, the ability to dismiss findings with documented reasons (essentially notes for future reviewers to triage analysis), and comma-separated and Markdown exports for easy import into existing audit systems.
[3]
Anthropic's Powerful New Cybersecurity Tool Is Designed to Find Vulnerabilities in Your Code -- and Patch Them
The AI giant announced on Thursday that Claude Security is in public beta for Claude Enterprise customers across the world to use to defensively scan their own code for vulnerabilities; it can also suggest and deploy patches. Anthropic announced service partners including Accenture, BCG, Deloitte, Infosys, and PwC, which the company says are already deploying Claude to ramp up enterprise security. "To combat AI-fueled cyber threats, our clients need advanced solutions they can deploy today, not tomorrow," global lead of Accenture Cybersecurity Harpreet Sidhu said in a statement. "With this powerful model, Accenture is already delivering mission-critical cyber defenses at scale, helping organizations move quickly from adoption to immediate implementation." The launch of Claude Security follows on the heels of reports that Claude Mythos, Anthropic's most powerful and heavily guarded model to-date, has demonstrated tremendous capabilities in identifying and exploiting software vulnerabilities. (Last week, Anthropic confirmed it is "investigating a report" that Mythos has already been accessed by unauthorized users, despite its very limited preview release.)
[4]
Anthropic launches Claude Security in public beta for enterprise customers
Anthropic has launched Claude Security in public beta, an AI-powered tool for enterprise security teams to scan codebases for vulnerabilities and generate patches. Powered by Claude Opus 4.7, the product reasons through code like a human researcher, tracing data flows and mapping component interactions. This offering aims to enhance code security by identifying bugs missed by traditional tools. Anthropic has launched Claude Security in public beta, giving enterprise security teams an AI-powered tool to scan codebases for vulnerabilities and automatically generate patches. The product is powered by Claude Opus 4.7 and is rolled out to Claude Enterprise customers globally, with access for Team and Max subscribers to be launched soon. It was first released as Claude Code Security in research preview in February, and hundreds of organisations have since used it to surface bugs that existing tools had missed for years. Shares of companies in the cyber security solutions space nosedived after Anthropic unveiled the tool. Unlike traditional scanners that match against known vulnerability patterns, Claude Security reasons through code the way a human researcher would. It traces data flows and maps how components interact across files and modules. A multi-stage validation pipeline then verifies each finding independently before it reaches an analyst, with every result assigned a confidence and severity rating. From there, users can move directly into a Claude Code session to review and apply a fix, with full context on the issue's likely impact and reproduction steps. This is part of Anthropic's wider push to make frontier AI capabilities available to defenders. It sits alongside new cyber safeguards built into Opus 4.7, which automatically detect and block high-risk cybersecurity requests, and Project Glasswing, Anthropic's initiative to protect critical software infrastructure. Technology partners including CrowdStrike, Palo Alto Networks, SentinelOne, Trend.ai, and Wiz are integrating Opus 4.7 into their platforms.
[5]
Anthropic Launches Claude Security: 5 Things To Know
The public beta of Claude Security for Claude Enterprise customers is aimed at enabling discovery of code vulnerabilities and generation of fixes. Anthropic announced Thursday it's moving Claude Security, formerly known as Claude Code Security, into public beta to enable rapid AI-powered vulnerability discovery and remediation. The launch follows the widely discussed disclosure about Anthropic's Claude Mythos Preview earlier this month, though the Claude Security offering does not leverage Mythos. [Related: How CISOs Need To Prepare For The Claude Mythos Era Of Cyberattacks: Experts] "Today's models are already highly effective at finding flaws in software code," Anthropic said in a blog post Thursday. "The next generation will be more capable still, and will be particularly effective at autonomously exploiting these flaws." What follows are five things to know about Anthropic's launch of Claude Security. Availability For Enterprise Customers Anthropic said that it is opening up availability of its Claude Security offering more broadly with its move from limited research preview -- which saw the tool tested by "hundreds of organizations of all sizes" -- into public beta. The public beta is available for all Claude Enterprise customers, the company said. Claude Team and Max customers are not yet able to access the offering, though Anthropic said that access for customers on those tiers is "coming soon." The offering, under the previous name of Claude Code Security, was originally announced in late February. Claude Mythos Not Included Following Anthropic's announcement about its unreleased Claude Mythos Preview earlier this month, the security industry has signaled that a massive push is needed around vulnerability management and hardening environments against a potentially massive spike in cyberattacks from the use of similar capabilities. Anthropic disclosed on April 7 that Claude Mythos Preview points to the fact that "AI models have reached a level of coding capability where they can surpass all but the most skilled humans at finding and exploiting software vulnerabilities." However, Claude Mythos Preview will remain only available to participants in the company's Project Glasswing initiative, with the model not being utilized for Claude Security, Anthropic said. Opus 4.7 Is The Basis Instead of Claude Mythos Preview, Anthropic said that its recently debuted Opus 4.7 model will form the basis of the Claude Security offering. "Our cybersecurity efforts go beyond Glasswing," Anthropic said in a post Thursday. "With Claude Security, a much wider set of organizations can put our most powerful generally-available model, Claude Opus 4.7, to work across their codebases." Ultimately, "Opus 4.7 is among the strongest models available for finding and patching software vulnerabilities, and for discovering complex, context-dependent issues that might otherwise be missed," the company said. The offering "comes with scheduled and targeted scans, easier integration with audit systems, and improved tracking of triaged findings," Anthropic said. Focus On Remediation In addition to discovery vulnerabilities in code, Claude Security will also bring a focus on generating proposed fixes for those issues, Anthropic said. From its testing of Claude Security so far, Anthropic has learned that "time from scan to fix is the metric that matters." "Early users pointed to this consistently, with several teams going from scan to applied patch in a single sitting, instead of days of back-and-forth between security and engineering teams," the company said. Accenture, Infosys Among Users So Far On the list of organizations that have used Claude Security so far is consulting giant Accenture, No. 1 on CRN's Solution Provider 500 for 2025, as well as Infosys, No. 8 on CRN's Solution Provider 500. Other organizations that have used the offering, which were listed by Anthropic, include Deloitte and PwC. The companies are "working alongside enterprise security organizations to deploy Claude-integrated security solutions for vulnerability management, secure code review, and incident response programs," Anthropic said in its post. In terms of vendors, Anthropic pointed to partnerships with CrowdStrike, Microsoft, Palo Alto Networks, SentinelOne, TrendAI and Google Cloud-owned Wiz, which are "integrating Opus 4.7's capabilities into the security platforms that enterprises already run on today," the company said.
[6]
Anthropic Launches Claude Security Amid Mythos Concerns
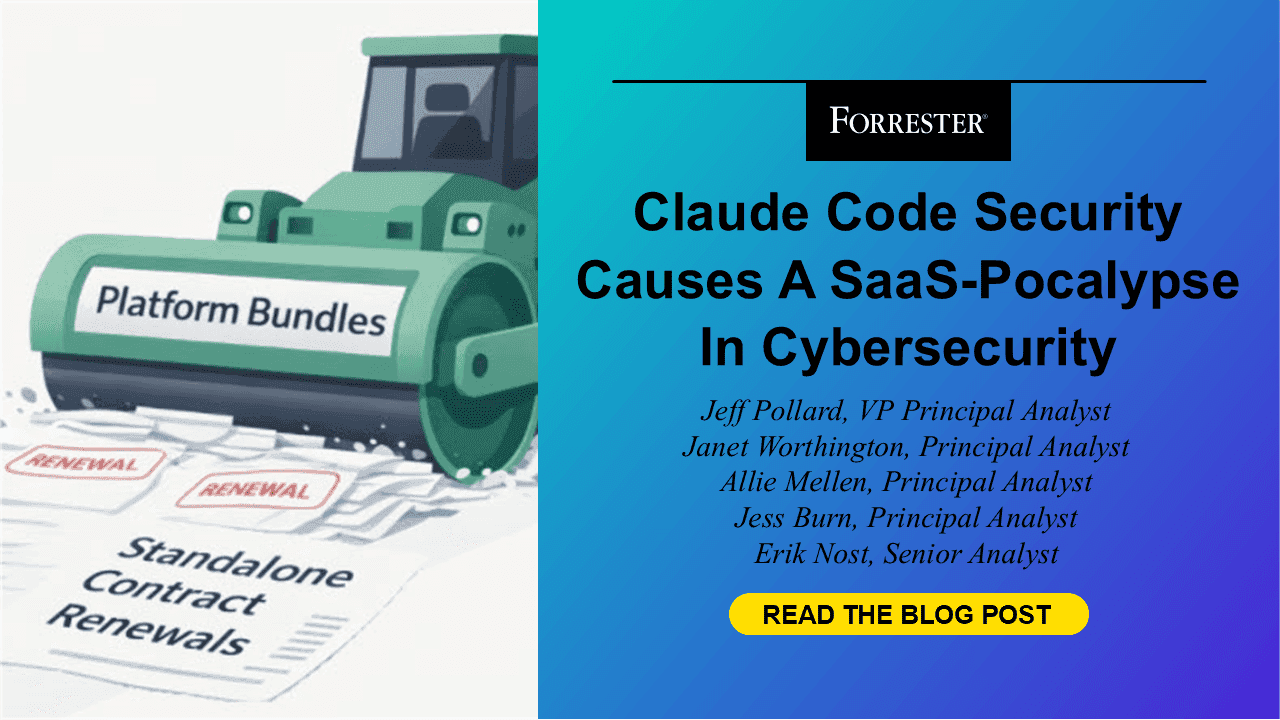
Anthropic has launched Claude Security, a defensive vulnerability scanner for enterprise codebases, three weeks after its most powerful model Mythos alarmed governments worldwide including India. The tool runs on Opus 4.7, a model Anthropic deliberately built to be less capable than Mythos on cybersecurity tasks. It does not address Mythos-level vulnerabilities. Does it address Mythos? Mythos is Anthropic's most powerful model, capable of finding and exploiting software vulnerabilities autonomously across major operating systems and browsers, including bugs hidden for decades. Anthropic restricted it to roughly 40 companies under Project Glasswing, a cross-industry cybersecurity initiative, because of the threat it poses if misused. On the day Mythos launched, a Discord group guessed its URL from Anthropic's naming conventions, exploited contractor credentials, and accessed the model through a third-party vendor environment, raising questions about Anthropic's ability to contain it. Anthropic said it is investigating the incident and found no impact on its core systems. MediaNama founder Nikhil Pahwa identified the core structural problem in Reasoned last week: "A tool that compresses attack timelines without compressing defense timelines increases systemic risk before it improves security." Pahwa also flagged the institutional gap Claude Security does not close: "Vulnerabilities can now be surfaced at machine speed, while the systems responsible for fixing them still move through human, institutional timelines, often with the primary objective of protecting their reputation." How far behind is Opus 4.7? Anthropic has stated that it deliberately reduced Opus 4.7's cyber capabilities during training compared to Mythos. On CyberGym, a UC Berkeley benchmark for cybersecurity capability, Mythos scored 83.1% against Opus 4.7's 73.1%. On the Firefox 147 exploit benchmark, Mythos produced 181 working exploits, code that actively takes advantage of a vulnerability to attack a system, compared to just 2 for Opus 4.6, a 90x gap. Anthropic calls Opus 4.7 the first model on which it has tested new cyber safeguards before any broader Mythos release. What Claude Security is: Claude Security gives defenders a way to find and patch vulnerabilities in their own code before attackers using Mythos-grade tools find them first. Teams scan their codebase directly from the Claude.ai sidebar with no Application Programming Interface (API) setup or custom agent build required. Currently only GitHub-hosted code repositories, where teams store and manage their software code, are supported. Access is available now to Claude Enterprise customers; while Team and Max customers get access soon. Claude Security reads source code, traces how data moves across different parts of the code, and reasons about how components interact. It generates a confidence rating for each finding, explains its severity, and produces a suggested patch that teams can work through in Claude Code. It does not match against a list of known bugs. Public beta features: Partners: Technology partners embedding Opus 4.7 into their existing enterprise security platforms: Services partners deploying Claude-integrated security solutions for enterprises: "This is not AI simply augmenting security," said Satish H.C., EVP and chief delivery officer at Infosys, in a statement to SecurityWeek. "It is AI redefining how enterprises defend themselves." India still locked out of Glasswing: No Indian company, bank, government agency, or telecom operator has secured admission to Project Glasswing. Ministry of Electronics and Information Technology (MeitY) Secretary S. Krishnan confirmed on April 28 that the government is still working out logistics with US authorities to include Indian entities. Nasscom has written to Anthropic arguing that Indian firms maintain critical code used by organisations worldwide and must be included. No resolution has been announced. Finance Minister Nirmala Sitharaman chaired a meeting on April 23 with Reserve Bank of India (RBI), National Payments Corporation of India (NPCI), Indian Banks' Association (IBA), and Indian Computer Emergency Response Team (CERT-In) officials, calling the Mythos threat "unprecedented." CERT-In has issued a high-severity advisory directing organisations to treat every critical vulnerability as exploitable within hours of disclosure, not weeks. Airtel and Vodafone Idea are reviewing their network software vendors' security practices. India's 2018 data localisation rules create a direct compliance conflict that remains unresolved: payment system providers must store all transaction data on servers within India, while Mythos runs on strictly controlled US-based servers. NPCI has not publicly addressed this. What Claude Security changes, and what it does not: Infosys, as a named services partner, can now deploy Claude Security to enterprise clients in India, giving Indian organisations an indirect path to Opus 4.7-powered vulnerability scanning. Indian companies still lack Mythos access, Glasswing membership, and a resolution to the data localisation conflict that blocks NPCI from using the model even if access comes through. Pahwa set out the geopolitical dimension plainly in Reasoned: "Strategic technologies do not distribute their benefits evenly, even when their risks are universal. The strategic benefit flows first to the US and its allies. Mythos is built by a US company, access is gated by that company, and the capability is explicitly framed as part of maintaining technological lead. Meanwhile everyone is vulnerable." Pahwa drew an analogy to COVID-era vaccine distribution: "It is important to watch who gets access to the vaccines first." Indian policymakers, banks, and IT firms face the same unresolved question Mythos raised three weeks ago: how to defend against a weapon they cannot access, using a tool that is deliberately less capable than the weapon.
Share
Copy Link
Anthropic has moved Claude Security into public beta for Enterprise customers worldwide, offering an AI-powered cybersecurity tool that scans entire codebases for vulnerabilities and generates targeted patches. Powered by Claude Opus 4.7, the tool reasons through code like a security researcher, tracing data flows and identifying bugs that traditional scanners have missed for years.
Anthropic Brings Claude Security to Enterprise Customers
Anthropic has announced the public beta launch of Claude Security, an AI-powered cybersecurity tool designed to help enterprise security teams scan codebases for vulnerabilities and generate targeted patches
1
. The tool is now available to Claude Enterprise customers globally, with access for Team and Max-tier users coming soon2
. Originally introduced as Claude Code Security in research preview in February, hundreds of organizations have already used it to discover and fix exploits in production code, including software vulnerabilities that existing tools had missed for years4
.
Source: Inc.
How Claude Opus 4.7 Model Powers Vulnerability Detection
Claude Security is powered by the Claude Opus 4.7 model, which Anthropic describes as "among the strongest models available for finding and patching software vulnerabilities"
5
. Unlike traditional scanners that match against known vulnerability patterns, the tool reasons about code the way a security researcher does, tracing data flows, reading source code, and examining how components interact across files and modules1
. This approach enables the system to discover complex, context-dependent issues that might otherwise be missed. A multi-stage validation pipeline verifies each finding independently before it reaches an analyst, with every result assigned a confidence rating and severity rating4
.
Source: ZDNet
From Scan to Fix: Accelerating Remediation for Cybersecurity Defenders
Anthropic emphasizes that "time from scan to fix is the metric that matters," with early users reporting they can go from scan to applied patch in a single sitting instead of days of back-and-forth between security and engineering teams
5
. Once Claude Security identifies an issue, users can move directly into a Claude Code session to review and apply a fix with full context on the issue's likely impact and reproduction steps4
. The tool generates patches and fixes that enable organizations to find and fix software vulnerabilities at scale2
. After feedback from the research preview, Anthropic added scheduled scans for ongoing coverage, the ability to dismiss findings with documented reasons, and comma-separated and Markdown exports for easy import into existing audit systems2
.Related Stories
Enterprise Partnerships and Platform Integrations
Service partners including Accenture, Deloitte, Infosys, and PwC are already deploying Claude to ramp up enterprise security
3
. Harpreet Sidhu, global lead of Accenture Cybersecurity, stated that "to combat AI-fueled cyber threats, our clients need advanced solutions they can deploy today, not tomorrow"3
. Technology partners including CrowdStrike, Palo Alto Networks, SentinelOne, Trend.ai, Wiz, and Microsoft are integrating Opus 4.7 into their cybersecurity platforms2
5
.Broader Cyberdefense Strategy and Security Safeguards
Claude Security sits alongside Anthropic's broader cyberdefense initiatives, including Project Glasswing, which brings together technology partners to secure the world's production software using the Mythos model
2
. However, Claude Security does not leverage the Mythos model, which remains available only to Project Glasswing participants5
. To prevent misuse, Opus 4.7 includes new cyber safeguards that automatically detect and block requests suggestive of prohibited or high-risk cybersecurity uses, such as mass data exfiltration or ransomware code development1
. The model also blocks activities with legitimate defensive applications, though cybersecurity researchers approved to join Anthropic's Cyber Verification Program gain access to AI capabilities in this restricted area1
. This dual approach aims to make frontier AI capabilities available to defenders while limiting access for potential attackers.References
Summarized by
Navi
[2]
Related Stories
Anthropic Introduces Automated Security Reviews in Claude Code to Address AI-Generated Vulnerabilities
07 Aug 2025•Technology

Anthropic's Claude Code Security triggers massive cybersecurity stocks selloff amid AI disruption
20 Feb 2026•Technology
Anthropic's Claude Opus 4.6 finds 500+ security flaws, sparking dual-use concerns
06 Feb 2026•Technology