Security researcher exposes new Windows Recall flaw, but Microsoft says it's not a vulnerability
5 Sources
[1]
"TotalRecall Reloaded" tool finds a side entrance to Windows 11's Recall database
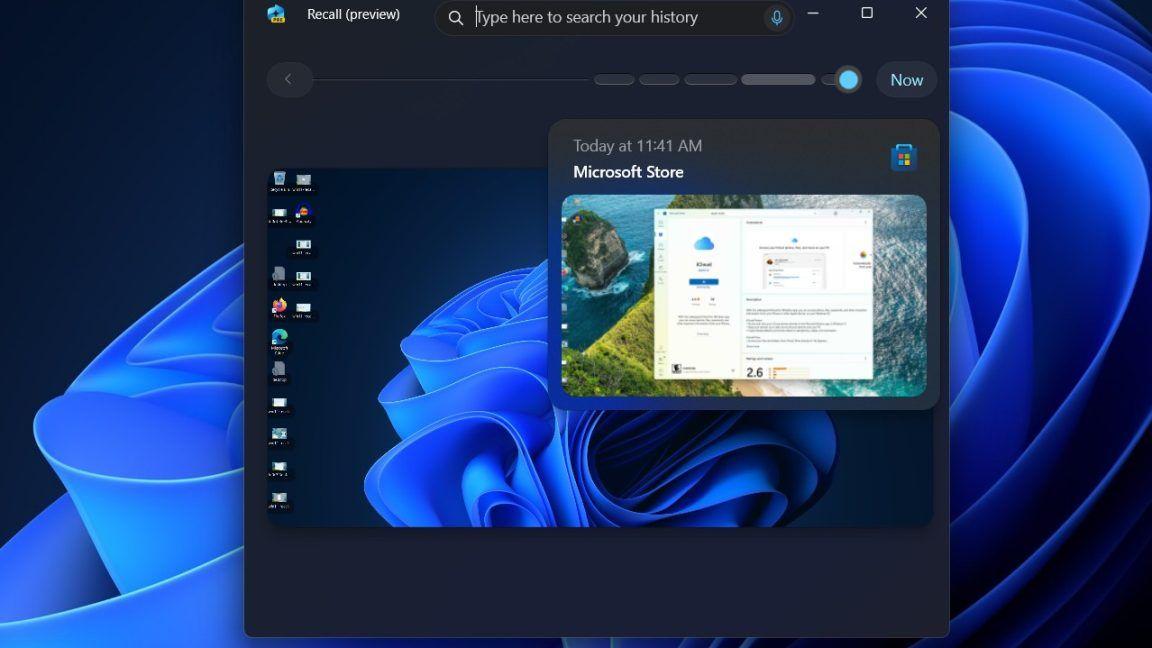
Two years ago, Microsoft launched its first wave of "Copilot+" Windows PCs with a handful of exclusive features that could take advantage of the neural processing unit (NPU) hardware being built into newer laptop processors. These NPUs could enable some AI and machine learning features that could be run locally rather than in someone's cloud, theoretically enhancing security and privacy. One of the first Copilot+ features was Recall, a feature that promised to track all your PC usage via screenshot to help you remember your past activity. But as originally implemented, Recall was neither private nor secure; the feature stored its screenshots plus a giant database of all user activity in totally unencrypted files on the user's disk, making it trivial for anyone with remote or local access to grab days, weeks, or even months of sensitive data, depending on the age of the user's Recall database. After journalists and security researchers discovered and detailed these flaws, Microsoft delayed the Recall rollout by almost a year, substantially overhauling its security. All locally stored data would now be encrypted and viewable only with Windows Hello authentication; the feature now did a better job detecting and excluding sensitive information, including financial information, from its database; and Recall would be turned off by default, rather than enabled on every PC that supported it. The reconstituted Recall was a big improvement, but having a feature that records the vast majority of your PC usage is still a security and privacy risk. Security researcher Alexander Hagenah was the author of the original "TotalRecall" tool that made it trivially simple to grab the Recall information on any Windows PC, and an updated "TotalRecall Reloaded" version exposes what Hagenah believes are additional vulnerabilities. The problem, as detailed by Hagenah on the TotalRecall GitHub page, isn't with the security around the Recall database, which he calls "rock solid." The problem is that, once the user has authenticated, the system passes Recall data to another system process called AIXHost.exe, and that process doesn't benefit from the same security protections as the rest of Recall. "The vault is solid," Hagenah writes. "The delivery truck is not." The TotalRecall Reloaded tool uses an executable file to inject a DLL file into AIXHost.exe, something that can be done without administrator privileges. It then waits in the background for the user to open Recall and authenticate using Windows Hello. Once this is done, the tool can intercept screenshots, OCR'd text, and other metadata that Recall sends to the AIXHost.exe process, which can continue even after the user closes their Recall session. "The VBS enclave won't decrypt anything without Windows Hello," Hagenah writes. "The tool doesn't bypass that. It makes the user do it, silently rides along when the user does it, or waits for the user to do it." A handful of tasks, including grabbing the most recent Recall screenshot, capturing select metadata about the Recall database, and deleting the user's entire Recall database, can be done with no Windows Hello authentication. Once authenticated, Hagenah says the TotalRecall Reloaded tool can access both new information recorded to the Recall database as well as data Recall has previously recorded. Bug or not, Recall is still risky For its part, Microsoft has said that Hagenah's discovery isn't actually a bug and that the company doesn't plan to fix it. Hagenah originally reported his findings to Microsoft's Security Response Center on March 6, and Microsoft officially classified it as "not a vulnerability" on April 3. "We appreciate Alexander Hagenah for identifying and responsibly reporting this issue. After careful investigation, we determined that the access patterns demonstrated are consistent with intended protections and existing controls, and do not represent a bypass of a security boundary or unauthorized access to data," a Microsoft spokesperson told Ars. "The authorization period has a timeout and anti-hammering protection that limit the impact of malicious queries." Regardless of Recall's underlying security, Recall can still constitute a major security and privacy risk. Anyone with access to your PC and your Windows Hello fallback PIN can access your database and everything in it, and even though Recall's content filters do a decent job excluding things like sensitive financial information, someone with access to your system could still see all kinds of emails, messages, web activity, and other stuff that you'd prefer not to share. Given the sheer amount of information that Recall can record, it still feels like a whole lot of potential downside for a pretty narrow and limited upside. The feature's riskiness has prompted some app developers to take matters into their own hands. The Signal Messenger app on Windows forces Recall to ignore it by default, using a flag that's normally intended to keep DRM-protected content out of the Recall database. The AdGuard ad blocker, the Brave browser, and others have implemented similar workarounds.
[2]
Windows 11's Recall tool has been cracked open again, and Microsoft doesn't see that as a problem
* Recall's vault is solid, but its delivery path exposes decrypted screenshots, OCR text, and metadata in AIXHost.exe. * TotalRecall Reloaded injects into AIXHost.exe via COM calls to grab decrypted data -- no admin, no kernel exploit needed. * The researcher alerted Microsoft first, but the company claims Recall access aligns with intended protections and timeouts limit abuse. Do you recall the old Recall drama? Back in June 2024, we caught wind that a researcher spotted Windows 11's AI-powered history feature, Recall, storing all of its findings in plain text on people's PCs. They believed that, if the tool was allowed to roll out for general use, hackers could very easily harvest these files, storing sensitive data. People's names, addresses, payment details, and everything else people typically handle on their PCs would be up for grabs. Microsoft rightfully delayed the Recall rollout, bringing it back to the workshop so it could better reinforce how Recall stores its data so that hackers couldn't get at the data. The bad news is, someone has found a new attack vector that hits the 'messengers' going to and from the Recall vault. The good news is, you shouldn't panic just yet; in fact, Microsoft says it doesn't even see a problem. I found a NotebookLM, Obsidian, and Anki killer, and studying will never be the same Three tools replaced by one. Posts 2 By Mahnoor Faisal TotalRecall Reloaded just cracked open Recall...again Third time's the charm? As reported by The Verge, cybersecurity pro Alexander Hagenah is back at it again. We last saw him during the original Recall rollout, where he created a tool called TotalRecall that could harvest data stored from the feature. It was one of the reasons Microsoft went back to the drawing board with Recall. Now, with the new and improved Recall, Hagenah noticed that, sure enough, the 'vault' that Recall uses to save its data is now ironclad. Unfortunately, as Hagenah puts it, "The vault is solid. The delivery truck is not." As such, he has released TotalRecall Reloaded, a new method to harvest data from Microsoft's AI tool. Here's how it works: AIXHost.exe, the process that renders the Recall timeline, has no PPL, no AppContainer, no code integrity enforcement. Any process running as the logged-in user can inject code into it and call the same COM APIs the legitimate UI uses. Once the user authenticates with Windows Hello, decrypted screenshots, OCR text, and metadata flow through AIXHost.exe as live COM objects. TotalRecall Reloaded sits inside that process and extracts everything. No admin required. Standard user. No kernel exploit. No crypto bypass. Just COM calls. Sounds like a problem, right? Well, there's some good news. Hagenah is all about cybersecurity, so before he even released this tool to the public, he brought it up with Microsoft a month before to demonstrate how it works. The problem, however, is that Microsoft doesn't believe it to be that big of a deal. In a statement to The Verge after being informed of the exploit, David Weston, corporate vice president of Microsoft Security, said the following: "After careful investigation, we determined that the access patterns demonstrated are consistent with intended protections and existing controls, and do not represent a bypass of a security boundary or unauthorized access to data. The authorization period has a timeout and anti-hammering protection that limit the impact of malicious queries." Is Microsoft right, or will Hagenah's new tool pose a real privacy threat? It's hard to say from here. If you'd like to read more about TotalRecall Reloaded, check out its GitHub page, where you can download the tool and perhaps even give it a go on your own devices to see how easy or difficult it is to replicate what Hagenah achieved. Another developer joins Brave in the fight against Recall as AdGuard moves to protect user privacy The anti-Recall club just got a new member. Posts 6 By Mahnoor Faisal
[3]
One year after its rocky launch, Microsoft's Windows Recall still raises security red flags
Microsoft says its Recall app -- which captures and stores screen shots every few seconds -- is safe. Security researchers keep saying otherwise. Recall was originally billed as a "photographic memory" to store everything Windows users do on their computers. People could then see some of those screen shots at a later time by searching AI with plain-text queries such as red barn. (See illustration above.) Select members of Microsoft's exclusive Windows Insider program have had access to Recall for more than a year. Users of AI-enabled Copilot+ PCs started receiving Recall as an opt-in feature in April 2025, one year ago this month. But since its debut, experts have repeatedly demonstrated that hackers can access the data Recall stores. This raises questions about whether a tool that records your entire digital life can ever be adequately secured. The situation is creating uncertainty about Microsoft's plans to make Recall more widely available on all PCs. Alexander Hagenah, executive director of SIX -- a Zürich-based technology company that operates infrastructure for stock exchanges in Switzerland and Spain -- described Recall's security weaknesses in a LinkedIn post in April 2025. He also released an app he called TotalRecall that could "extract all captured windows and images taken by Recall ... nothing encrypted, no rocket science needed." Joining other researchers, the University of Pennsylvania's Office of Information Security released a warning on Apr. 14, 2025, about the version of Recall that was then available. The university's announcement stated that Recall "introduces substantial and unacceptable security, legality, and privacy challenges" [emphasis in the original]. The statement added that administrators of "Windows environments at Penn are strongly urged" to disable Recall. In response to criticisms such as these, Microsoft -- to its credit -- pulled back on its plans to roll out Recall to all Windows 11 PCs that met fairly high system requirements (including a neural processing unit and eight logical processors, according to an MS Learn document). Instead, the company announced in a blog update on June 13, 2024, that Recall would become available only to participants in the company's much smaller Windows Insider program. In the time since that decision, the fate of Recall has become even murkier. Journalist Zac Bowden wrote in a Windows Central blog post on Jan. 30, 2026, that Microsoft is "pulling back its Windows 11 AI push with a major Copilot and Recall rethink." The problem is that it's tough for software engineers to make data ultra-convenient for end users to access while simultaneously securing it so it's impervious to hackers. It's hard to remember that the company's original goal was ease of use, now that Microsoft's focus has changed to making the security of its screen-cap app impenetrable. Microsoft says Recall blurs images of credit-card numbers, bank passwords, and other personal data -- or doesn't store them at all. But security experts are still not convinced. After testing the latest version of Recall, Swiss technologist Hagenah recently issued a new proof-of-concept called "Total Recall Reloaded" on a GitHub page. In his comments, Hagenah said any malware running on a user's PC can copy every Recall screen shot as it passes through in-process memory: "No admin required. Standard user. No kernel exploit." Hagenah has not publicly disclosed some security holes, saying he's reported them to Microsoft and won't release the technical details until the Redmond company has fixed the problems. Already, malicious hackers have written code to take advantage of Recall's screen shots. The malware can access Recall's own memory to copy screen caps and send them to a faraway server. Hackers no longer need to write such code from scratch. (The procedure is described in a technical overview by cybersecurity writer Kevin Beaumont.) At this writing, fewer than 10% of Windows 11 PCs can enable and run the current version of Recall. Microsoft representatives responded to my inquiries about plans for the app's future availability by pointing to a Sept. 27, 2024, security update and an Apr. 25, 2025, blog post.
[4]
Cybersecurity experts raise the alarm over Windows Recall again: 'The vault door is titanium. The wall next to it is drywall'
Hacking tool supposedly creates "precisely the scenario Microsoft's architecture is supposed to restrict." Remember Windows Recall? The AI feature that essentially screenshots nearly everything you do on your PC in order to present users with a timeline of activity they can rewind back through? It was meant to be available on Copilot+ AI PCs from June 2024 but got, ahem, recalled a number of times amid cybersecurity concerns. The feature has since been redesigned, but security researchers are raising the alarm again. Windows Insiders have had access to the redesigned Recall since last year, but allegedly the more things change, the more they stay the same. Case in point, after already breaking the original Recall, security researcher Alexander Hagenah has created another tool that can expose the refreshed Recall's various vulnerabilities by extracting and displaying the data it captures (via The Verge). Microsoft previously described Recall's security model in a September 2024 blog post, sharing, "Recall snapshots and associated data are protected by secure VBS Enclaves." Basically, all of that potentially sensitive data is meant to be cordoned off in a "locked box that can only be accessed after permission is granted by the user through Windows Hello." Unfortunately, Hagenah says, "My research shows that the vault is real, but the trust boundary ends too early." Hagenah's tool is called TotalRecall Reloaded, but how does it work? Very simply, it will camp out quietly in the background of your desktop, and then ride the coat tails of your access to the Recall timeline when you next open the 'locked box' via a Windows Hello prompt. From there, TotalRecall Reloaded can reportedly snaffle the contents of the entire vault like a hydrocolloid bandage on a zit. Microsoft wrote back in 2024 that asking users for biometric credentials each time they want to access Recall would restrict "attempts by latent malware trying to 'ride along' with a user authentication to steal data." Unfortunately, Hagenah says his tool creates "precisely the scenario Microsoft's architecture is supposed to restrict." As such, Hagenah claims he responsibly disclosed his security research to Microsoft last month -- but this leads me to perhaps the most infuriating twist in this tale. According to Hagenah, Microsoft told him that what he found was 'not a vulnerability'. In a statement to The Verge, Microsoft Security's corporate vice president David Weston said, "We appreciate Alexander Hagenah for identifying and responsibly reporting this issue. After careful investigation, we determined that the access patterns demonstrated are consistent with intended protections and existing controls, and do not represent a bypass of a security boundary or unauthorized access to data. The authorization period has a timeout and anti-hammering protection that limit the impact of malicious queries." Given that Recall can hoard everything from browsing history, to whatever text may have crossed your screen in the form of emails, private messages, and so on, it may be difficult to understand Microsoft's stance here. Though in its view, this doesn't qualify as a vulnerability. At the risk of over-simplifying, TotalRecall Reloaded isn't forcing Windows to do anything it doesn't already do, and a fully fledged fix would likely involve overhauling the OS's foundations. Microsoft is also hoping that prompting for biometric credentials every time a user wants to use Recall will curtail malicious activity. To Microsoft's credit, Hagenah did praise Recall's "rock solid" VBS Enclave -- though the issue isn't that the 'locked box' has a dodgy door. "The fundamental problem isn't the crypto, the enclave, the authentication, or the PPL. It's sending decrypted content to an unprotected process for rendering," Hagenah says, "The vault door is titanium. The wall next to it is drywall."
[5]
Researcher Questions Windows Recall Security Again Due to This Reason
* Research highlights gaps in Recall's data access controls * Researcher says Recall data can be accessed after login * Microsoft says Recall behaviour aligns with system design TotalRecall Reloaded, a tool developed by cybersecurity researcher Alexander Hagenah, has raised fresh concerns about Microsoft's Windows Recall feature and how it handles sensitive user data. The research points to potential issues in how information is accessed after authentication, even though Microsoft had redesigned Recall with stronger protections. The company reportedly views the behaviour as part of its existing system design, but the findings highlight ongoing concerns about whether features that record user activity can remain both useful and secure. TotalRecall Reloaded Highlights Ongoing Windows Recall Security Concerns The Recall tool is built to pull data from Recall, an AI feature that takes regular snapshots of what appears on your screen so you can search through your past activity. Hagenah said his updated version can quietly run in the background and access that data once a user logs in through Windows Hello. Microsoft had reworked Recall after facing criticism earlier, adding stronger protections like encryption, secure enclaves and biometric authentication. The company had said these changes would stop malicious software from taking advantage of a user's login to access stored data. However, Hagenah explains that the protection does not fully work as intended. He said the system's secure storage is strong, but the boundary that controls how data is accessed breaks down too early. According to him, the tool can effectively follow a user's authentication process and then retrieve stored information. The data Recall stores go beyond simple screenshots. It can include on-screen text, messages, emails, documents, browsing activity, timestamps, and AI-generated context, building a detailed picture of how a user interacts with their device. Hagenah said he shared his findings with Microsoft in March 2026, along with the necessary technical details and code. He claims the company reviewed the report but did not consider it a security issue, stating that the behaviour aligns with how the system is meant to work and does not break any security boundaries. Microsoft also said that measures like time limits and protections against repeated access help reduce the risk. Hagenah, however, disagreed and argued that these safeguards can be bypassed. The Verge reported that the issue may stem from the way Recall delivers decrypted data to other processes after authentication. While the storage system itself remains secure, the method used to present that data could expose it to misuse. Despite the concerns, Hagenah acknowledged that several parts of Recall's redesigned security, including its encryption and authentication model, are robust, according to the aforementioned The Verge report. He suggested that further improvements are needed in how data is handled after it leaves the secure environment.
Share
Copy Link
A cybersecurity researcher has developed TotalRecall Reloaded, a tool that can extract decrypted data from Windows Recall by exploiting the AIXHost.exe process. Despite responsible disclosure, Microsoft claims the access patterns are consistent with intended protections and do not constitute a security vulnerability, sparking debate about whether features that record user activity can ever be adequately secured.
Windows Recall faces renewed security scrutiny
Windows Recall is under fire again. Security researcher Alexander Hagenah has released TotalRecall Reloaded, a tool that exposes what he believes are critical security and privacy risks in Microsoft's AI-powered feature designed for Copilot+ Windows PCs
1
. The feature, which captures screenshots every few seconds to create a searchable timeline of user activity recording, was delayed nearly a year after its original 2024 launch due to severe security flaws3
.
Source: GeekWire
Microsoft redesigned Recall with encryption, VBS Enclaves, and Windows Hello authentication to address initial concerns. But Hagenah's research suggests the security boundary ends too early in the data delivery chain
4
. While the vault storing Recall data remains "rock solid," the AIXHost.exe process that renders the timeline lacks the same protections1
.
Source: Ars Technica
How the TotalRecall Reloaded tool works
The TotalRecall Reloaded tool operates by injecting code into AIXHost.exe without requiring admin privileges or kernel exploit techniques
2
. It waits silently in the background until a user authenticates with Windows Hello to access their Recall timeline. Once user authentication occurs, the tool can intercept and extract decrypted screenshots, OCR text, and metadata flowing through the AIXHost.exe process1
.Hagenah describes the vulnerability with a vivid analogy: "The vault door is titanium. The wall next to it is drywall"
4
. The fundamental problem isn't the encryption or the secure enclave—it's that decrypted content gets sent to an unprotected process for rendering. This creates precisely the scenario Microsoft's architecture was supposed to restrict: malware riding along with legitimate user access to steal data4
.The tool can access both new information being recorded and previously stored data once authentication happens. Some tasks, including grabbing the most recent screenshot and deleting the entire Recall database, can even be performed without Windows Hello authentication
1
.Microsoft security response sparks debate
Hagenah responsibly disclosed his findings to Microsoft's Security Response Center on March 6, 2026. On April 3, Microsoft officially classified the issue as "not a vulnerability"
1
. David Weston, corporate vice president of Microsoft Security, stated that "the access patterns demonstrated are consistent with intended protections and existing controls, and do not represent a bypass of a security boundary or unauthorized access to data"4
.
Source: PC Gamer
Microsoft points to timeout periods and anti-hammering protection as safeguards that limit the impact of malicious queries
2
. However, Hagenah argues these protections can be bypassed, and the company's stance raises questions about data access controls for features that capture extensive user activity5
.The University of Pennsylvania's Office of Information Security released a warning on April 14, 2025, stating that Recall "introduces substantial and unacceptable security, legality, and privacy challenges," urging administrators to disable the feature
3
.Related Stories
What this means for users and the AI feature's future
The security vulnerability debate highlights a fundamental tension: making data ultra-convenient for users to access while simultaneously securing it against hackers proves extremely difficult
3
. Recall stores screenshots, emails, messages, web activity, browsing history, timestamps, and AI-generated context—building a detailed picture of how users interact with their devices5
.Anyone with access to a PC and the Windows Hello fallback PIN can potentially view this database. Even though Recall's content filters exclude sensitive financial information, the sheer amount of personal data it records creates significant privacy threat potential
1
. Malicious hackers have already written code to exploit Recall's memory and send screenshots to remote servers3
.Currently, fewer than 10% of Windows 11 PCs can run Recall, with the feature available only as an opt-in for Copilot+ PC users since April 2025
3
. Windows Insider program participants have had access for over a year. Microsoft's plans for wider availability remain unclear, with journalist Zac Bowden reporting in January 2026 that the company is "pulling back its Windows 11 AI push with a major Copilot and Recall rethink"3
.Some app developers are taking matters into their own hands. Signal Messenger forces Recall to ignore it by default, using a flag normally intended for different purposes
1
. The cybersecurity community continues watching whether Microsoft will address these concerns or if the feature's fundamental design makes adequate security impossible. For now, the gap between the secure vault and the vulnerable delivery mechanism remains a point of contention in the ongoing debate about AI features that monitor everything users do.References
Summarized by
Navi
[2]
[3]
Related Stories
Microsoft Recall AI App Continues to Raise Security Concerns Despite Updates
02 Aug 2025•Technology

Microsoft Relaunches Controversial Recall Feature for Copilot+ PCs Amid Privacy Concerns
26 Apr 2025•Technology

Microsoft's AI-Powered Recall Feature Fails to Protect Sensitive Information Despite Privacy Assurances
13 Dec 2024•Technology

Recent Highlights
1
Meta AI chatbot exploited by hackers to hijack high-profile Instagram accounts worth millions
Technology

2
Florida sues OpenAI and Sam Altman over ChatGPT safety, alleging AI harms linked to violence
Policy and Regulation

3
Nvidia RTX Spark chips power new AI laptops with up to 128GB memory and local agent capabilities
Technology

Recent Highlights
Today's Top Stories
News Categories