Hackers exploit Google Ads and Claude.ai shared chats to spread Mac malware
4 Sources
[1]
Hackers abuse Google ads, Claude.ai chats to push Mac malware
Attackers are abusing Google Ads and legitimate Claude.ai shared chats in an active malvertising campaign. Users searching for "Claude mac download" may come across sponsored search results that list claude.ai as the target website, but lead to instructions that install malware on their Mac. The campaign was spotted by Berk Albayrak, a security engineer at Trendyol Group, who shared his findings on LinkedIn. Albayrak identified a Claude.ai shared chat that presents itself as an official "Claude Code on Mac" installation guide, attributed to "Apple Support." The chat walks users through opening Terminal and pasting a command, which silently downloads and runs malware on their Mac. While attempting to verify Albayrak's findings, BleepingComputer landed on a second shared Claude chat carrying out the same attack through entirely separate infrastructure. The two chats follow an identical structure and social engineering approach but use different domains and payloads. Both chats were publicly accessible at the time of writing: The base64 instructions shown in the shared Claude chat download an encoded shell script from domains such as: The 'loader.sh' (served by the second link above) is another set of Gunzip-compressed shell instructions: This compressed shell script runs entirely in memory, leaving little obvious trace on disk. The variant BleepingComputer identified starts by checking whether the machine has Russian or CIS-region keyboard input sources configured. If it does, the script exits without doing anything, sending a quiet cis_blocked status ping to the attacker's server on its way out. Only machines that pass this check get the next stage: Before proceeding further, the script also collects the victim's external IP address, hostname, OS version, and keyboard locale, sending all of it back to the attacker. This kind of victim profiling before payload delivery suggests the operators are being selective about who they target. The script then pulls down a second-stage payload and runs it through osascript, macOS's built-in scripting engine. This gives the attacker remote code execution without ever dropping a traditional application or binary. The variant identified by Albayrak, however, appears to skip the profiling steps. It goes straight to execution. It harvests browser credentials, cookies, and macOS Keychain contents, packages them up, and exfiltrates them to the attacker's server. Researchers have identified this as a variant of the MacSync macOS infostealer: The briskinternet[.]com domain shown above in the variant identified by Albayrak appeared to be down at the time of writing. Malvertising has become a recurring delivery mechanism for malware. BleepingComputer has previously reported on similar campaigns targeting users searching for software like GIMP, where a convincing Google ad would list a legitimate-looking domain but take visitors to a lookalike phishing site instead. This campaign flips that, as there is no fake domain to spot. Both Google ads seen here point to Anthropic's real domain, claude.ai, since the attackers are hosting their malicious instructions inside Claude's own shared chat feature. The destination URL in the ad is genuine. It is not, however, the first time that attackers have abused AI platform shared chats this way. In December, BleepingComputer reported a similar campaign targeting ChatGPT and Grok users. Users should navigate directly to claude.ai for downloading the native Claude app, rather than clicking sponsored search results. The legitimate Claude Code CLI is available through Anthropic's official documentation and does not require pasting commands from a chat interface. It is good practice to generally treat any instructions asking you to paste terminal commands with caution, regardless of where those instructions appear to come from. BleepingComputer reached out to Anthropic and Google for comment prior to publishing.
[2]
Mac users beware -- scammers are hijacking Claude chats and Google ads to push malware
* Crooks abused Claude's "Shared Chats" feature to plant fake install instructions leading to infostealer infections * Fraudulent chats were promoted via Google Ads, showing authentic Claude URLs to trick Mac users * Campaign used ClickFix tactics, spoofed "Apple Support," and avoided targeting Russian‑language systems Cybercriminals are abusing legitimate Claude and Google Ads services to trick Mac users into installing infostealing malware on their devices, experts have warned. A new campaign was recently spotted, and disclosed, by security researcher Berk Albayrak on LinkedIn, concerning a feature called "Shared Claude Chats", which allows users to create clickable links of previous conversations they've had with the AI. That way, other people can view those specific chat sessions through a public URL. According to Albayrak, the hackers have created conversations in which the platform shows instructions on how to install Claude Code (a command-line coding assistant). However, the instructions are nothing but the standard ClickFix scam - they tell the user to bring up the Terminal and paste a command, which triggers a chain reaction resulting in an infostealer infection. Advertising the scam on Google The conversation was created by an account named "Apple Support", likely to increase its legitimacy. Those with a shaper eye, however, could easily spot the trick, since the chat has a disclaimer at the top, warning the content below might be "unverified or unsafe". But creating the fraudulent conversation is just half the process - victims must still somehow land there. That's where Google Ads come in. The crooks were able to purchase ads on Google's advertising network, meaning people searching for "Claude Code on Mac" would be served this chat at the very top of the search engine results page. To make matters worse, those who would hover over the link or double-check where it leads, would see "claude.ai" - the authentic Claude URL. Albayrak did not say how many people might have been compromised this way, but BleepingComputer found the malware does not work on computers with Russian language, suggesting that the miscreants are actively avoiding targeting Russians. Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds.
[3]
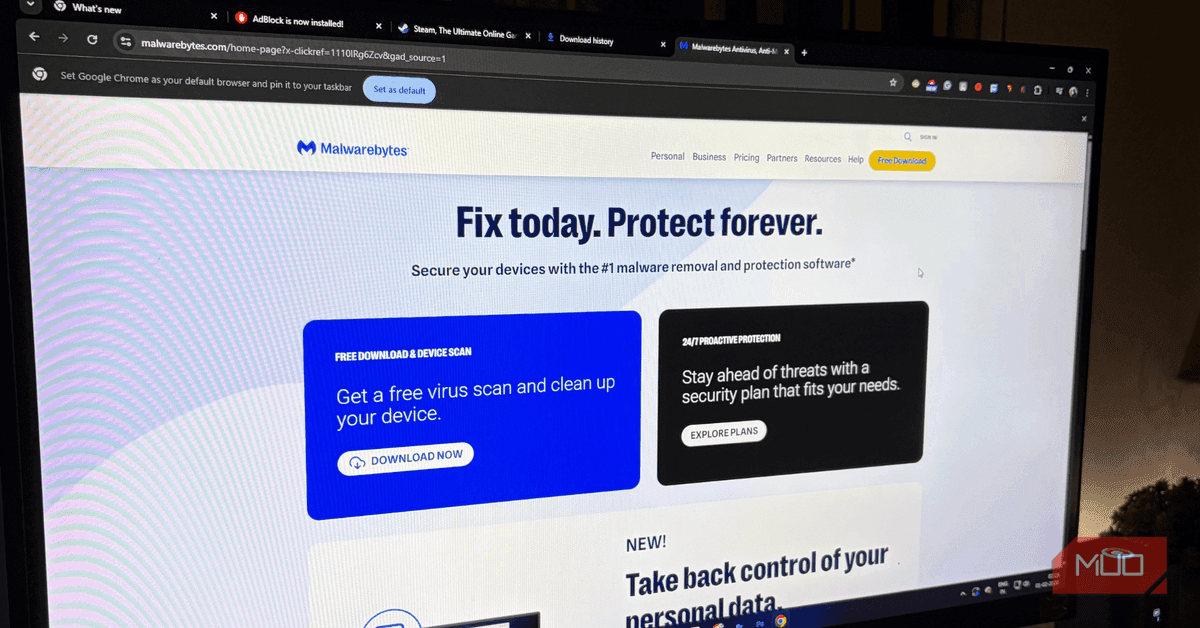
Malware is now hiding in Google search ads -- here's how to protect yourself
Outside of the office, Josh can be found digging into the latest video games, fantasy books, or tinkering with the newest features in Windows. A new malware campaign has been discovered hiding in people's Google search results when trying to find and download Claude's Mac app. It's a stark reminder of just how pervasive advertisements have become in our day-to-day lives, and why using an ad blocker can be a great way to protect yourself. Related Hackers are disguising malware as Claude Code, and it's easy to fall for the scam Be careful what links you follow Posts By Dave Schafer Malware has always hidden in ads But now they can appear directly in your search results Bad actors have become very good at making malicious downloads look legitimate and even inviting. Sometimes it might be a fake software update, while other times it's a full, convincing workup of a company's support website. And as is the case with a new malware currently making the rounds, it could even be the sponsored ad that appears at the top of your Google search results. This newest trend is picking up on the popularity of AI-powered apps like Claude, which has become huge thanks to the release of its Cowork function, which is great at automating your job, and Claude Code. The latest threat targets people looking to use Claude on Mac and was discovered by security engineer Berk Albayrak, who works with the Trendyol Group. Albayrak shared his findings on LinkedIn, noting that the malware-ridden ad pops up when users search for 'Claude download mac' on Google. If you searched for that term, and then clicked on the infected ad, it would lead you to a legitimate claude.ai page which has instructed for installing the malware embedded in the page. It's a very common way of delivering malware, as it asks those who click on it to paste a set of commands into Terminal, which then downloads the infected files to their device. But this campaign isn't just happening across one source, either, as BleepingComputer also discovered a second shared Claude chat being distributed in the same way. What makes malware like this latest Claude malware so terrifying for everyday people, is the fact that it looks to run entirely in your computer's memory, thus leaving little trace on your disk. That can make it harder to track down and remove. Ads have become a hotbed for malware Blocking them is one of the only ways to truly protect yourself There's no arguing that ads have become rampant on the internet. For many websites and creators, these are a way to keep the lights on. And our reliance on those sources to help drive income has made them a perfect way for threat actors to try to get some kind of gain from it. Subscribe to our newsletter for ad-based malware tips Keep your devices safe - subscribe to our newsletter for clear, practical coverage of ad-borne threats, ad-blocker recommendations, and steps to verify authentic app downloads so you can avoid malicious installers. Get Updates By subscribing, you agree to receive newsletter and marketing emails, and accept our Terms of Use and Privacy Policy. You can unsubscribe anytime. If you don't use an ad blocker already -- and there are good reasons not to, considering YouTube has launched several campaigns against their use -- it might not be a bad idea to set one up. There are several browser extensions you can use to block annoying ads, and most ad blockers have a way to allowlist different sites, so you can still block out the bad while supporting the good. If you're using an Android phone, then you can change DNS settings to block ads and other annoying content, too. Some browsers, like Opera (pictured above) even come with built-in ad blocking systems. Claude Developer Anthropic PBC Price model Free, subscription available Claude is an advanced artificial intelligence assistant developed by Anthropic. Built on Constitutional AI principles, it excels at complex reasoning, sophisticated writing, and professional-grade coding assistance. See at App Store See at Google Play Store See at Claude Expand Collapse Finally, if you're looking for an official download for an app, it's always best to start at the source. And, if a page asks you to paste a command into Terminal on Mac or Command Prompt on Windows, then it's likely not something you'll want to follow through with, as it could put your device at risk.
[4]
Google Ads are not safe anymore? Hackers can access your device if you ignore this
Users should avoid unknown ads, check website links carefully, and never paste unfamiliar commands. Google Ads are back in the limelight, as a new cyber threat was recently discovered by experts who found that the malicious software had targeted those searching for the Claude AI application on their Macs. The threat came up in Google-sponsored ads, which made it seem credible to regular users. This information was revealed by Berk Albayrak, a security engineer at Trendyol Group, on his LinkedIn page. The attack highlights a growing problem where hackers misuse online advertisements to spread harmful software. Experts now warn that clicking the wrong sponsored result could expose personal data, compromise devices, and put users at serious security risk online today. The latest malware campaign targeted users searching 'Claude download mac' on Google. According to a LinkedIn post shared by Berk Albayrak, the sponsored ad looked genuine and even redirected users to a legitimate-looking Claude AI page. However, users were then instructed to paste commands into the Mac Terminal app. Those commands silently downloaded malware onto the device. Reports suggest the harmful software mainly runs in memory, making it harder to detect or remove. Cybersecurity publication BleepingComputer also reportedly found another similar malicious Claude-related campaign. Many people have a tendency to believe the initial few hits on Google searches, particularly those sponsored by businesses. Hackers have exploited this tendency by designing ads that mimic official business pages. What makes this attack more worrying is its stealthy nature. Since the malware leaves limited traces on storage drives, users may not realise their system has already been compromised. Experts say these scams are becoming more common because online advertising platforms offer attackers easy visibility. Security engineer Berk Albayrak, who works with Trendyol Group, publicly shared screenshots and details of the malicious ad campaign on LinkedIn. His post warned users to avoid blindly trusting sponsored search results while downloading software. The post has since gained attention among cybersecurity professionals and everyday internet users alike. Follow the easy steps below to stay safe against the Google Ads scam:
Share
Copy Link
Security researchers have uncovered an active cybercrime campaign targeting Mac users through fraudulent Google Ads and Claude.ai's legitimate shared chat feature. Attackers are creating fake installation guides that trick users into running Terminal commands, silently downloading infostealing malware onto their devices. The campaign exploits trust in sponsored search results and authentic Claude URLs.
Hackers Abuse Google Ads to Target Mac Users
A sophisticated cybercrime campaign targeting Mac users has emerged, exploiting both Google Ads and Claude.ai's legitimate features to distribute Mac malware. Security engineer Berk Albayrak from Trendyol Group first identified the threat, revealing that users searching for "Claude mac download" encounter sponsored search results that appear to link to claude.ai but actually lead to malicious instructions
1
. What makes this attack particularly deceptive is that the Google Ads genuinely point to Anthropic's real domain, since attackers are hosting their malicious content inside Claude's Shared Chats feature2
.
Source: Digit
Claude's Shared Chats Feature Weaponized for Malware Distribution
The attackers created fraudulent conversations within Claude.ai that present themselves as official "Claude Code on Mac" installation guides, often attributed to "Apple Support" to increase legitimacy
1
. These shared chats walk users through opening Terminal and pasting commands that silently download and execute infostealing malware on their devices. BleepingComputer identified a second shared Claude chat carrying out the same attack through entirely separate infrastructure, indicating the campaign's scope extends beyond a single operation1
. The malware hiding in Google search ads operates as an in-memory threat, running entirely in memory and leaving little obvious trace on disk, making detection and removal significantly more challenging3
.
Source: BleepingComputer
How the Infostealer Operates and Targets Victims
The base64 instructions shown in the shared Claude chat download an encoded shell script that runs through osascript, macOS's built-in scripting engine, giving attackers remote code execution without dropping a traditional application or binary
1
. Before proceeding with payload delivery, one variant checks whether the machine has Russian or CIS-region keyboard input sources configured, exiting without action if detected and sending a "cis_blocked" status ping to the attacker's server1
. The script collects the victim's external IP address, hostname, OS version, and keyboard locale, sending all data back to the attacker before delivering the next stage. This victim profiling suggests operators are selective about their targets1
. The infostealer harvests browser credentials, cookies, and macOS Keychain contents, packages them up, and exfiltrates everything to the attacker's server, identified as a variant of the MacSync macOS infostealer1
.Related Stories
Why Malicious Ads Pose Growing Security Risks
This cyber threat represents a troubling evolution in malvertising tactics. Unlike previous campaigns where convincing Google Ads would list legitimate-looking domains but redirect visitors to lookalike phishing sites, this campaign flips that approach entirely
1
. There is no fake domain to spot, as both Google Ads point to Anthropic's authentic domain. The destination URL in the sponsored search results is genuine, making it nearly impossible for average users to distinguish malicious from legitimate advertisements2
. This isn't the first time attackers have abused AI platform shared chats this way—in December, BleepingComputer reported a similar campaign targeting ChatGPT and Grok users1
. Online advertisements have become a hotbed for distributing harmful software because advertising platforms offer attackers easy visibility and user trust3
.Protecting Against Terminal Commands and Sponsored Results
Users should navigate directly to official sources rather than clicking sponsored search results when downloading software
1
. The legitimate Claude Code CLI is available through Anthropic's official documentation and does not require pasting Terminal commands from a chat interface. Security experts recommend treating any instructions asking users to paste commands with extreme caution, regardless of where those instructions appear to originate1
. Implementing ad blockers can provide an additional layer of protection, as many browser extensions allow users to block malicious ads while allowlisting trusted sites3
. Some browsers like Opera even come with built-in ad blocking systems3
. As this campaign demonstrates the stealthy nature of in-memory malware and bypassing detection mechanisms, Mac users must remain vigilant about verifying installation instructions and avoiding unfamiliar commands that could compromise their devices and expose personal data4
.
Source: MakeUseOf
References
Summarized by
Navi
[1]
Related Stories
Hackers disguise infostealer malware as Claude Code and OpenClaw to target developers
18 Mar 2026•Technology

Fake Claude Code sites spread malware through cloned install guides targeting developers
07 Mar 2026•Technology
Attackers exploit ChatGPT and Google ads to spread AMOS infostealer targeting macOS users
11 Dec 2025•Technology

Recent Highlights
1
Anthropic overtakes OpenAI as most valuable AI startup with $965 billion valuation
Business and Economy
2
Pope Leo XIV releases major AI encyclical calling for 'disarmament' of artificial intelligence
Policy and Regulation

3
Apple's Siri overhaul for iOS 27 brings Gemini integration and standalone app to compete with ChatGPT
Technology